- Cisco Community
- Technology and Support
- Networking
- Switching
- Re: QoS configuration - set and markdown in one map
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2019 02:02 PM - edited 05-14-2019 03:03 PM
Hello,
I'm not sure how to proceed with my problem, probabely I my idea is wrong, because I didn't found any examples of such confiugration, but then, what is the right way?
I'm going to classify traffic from untrusted source. So for example I would set AF21 for a specific application, that matches ACL21. But if the traffic exeeds CIR, I'm going to mark down to AF22 and if the traffic exeeds PIR, then to AF23.
Incoming packets have a DSCP value of 0, so I have in any case to set an AF value.
So what I did:
ip access-list extended ACL-AF21 permit tcp any range 50040 50059 any range 40803 49151 permit udp any range 50040 50059 any range 40803 49151 class-map match-any CM-AF2x match access-group name ACL-AF21 policy-map MARK2x class CM-AF2x police cir percent 10 pir percent 20 be 200 ms conform-action transmit exceed-action set-dscp-transmit af22 violate-action set-dscp-transmit af23 set dscp af21 end
Can it work as I expect, to set AF21 for all packets <= 10% BW, AF22 for all packets <= 20% BW and AF23 for all other packts? Will it first set AF21 and then run two-rate three color policer?
At the end, I'm going to use an egress policy, with DSCP based WRED and queue-limits for AF2x; but to first of all, I have to mark incoming packets with AF2x values.
May be it is better to mark all traffic matching ACL-AF21 with AF21 and then set in the output policy:
class-map match-any CM-AF21
match dscp AF21
policy-map OUTPUT class CM-AF21 police cir percent 10 pir percent 20 be 200 ms conform-action transmit exceed-action set-dscp-transmit af22 violate-action set-dscp-transmit af23 bandwidth remaining percent 10 queue-limit dscp af21 percent 100 queue-limit dscp af22 percent 90 queue-limit dscp af23 percent 80 queue-buffers ratio 10 end
could it be the better way?
btw. I just noticed, that cat3650 doesn't offer "random-detect dscp" command in policy map configuration menu - is there another way to adjust WRED?
What is the better way to achive my goal?
Thanks
Solved! Go to Solution.
- Labels:
-
Catalyst 3000
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-23-2019 02:46 AM
Hello,
thanks for answers, the solution was an update to version 16 (everest), there is possible to set "conform-action set-dscp-transmit <value>"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2019 03:03 PM
If it doesn't work as desired, can you use an ingress policy to mark all traffic in that class to AF21, allowing the policer to down mark the overrate traffic?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-14-2019 03:16 PM - edited 05-14-2019 03:22 PM
Hi,
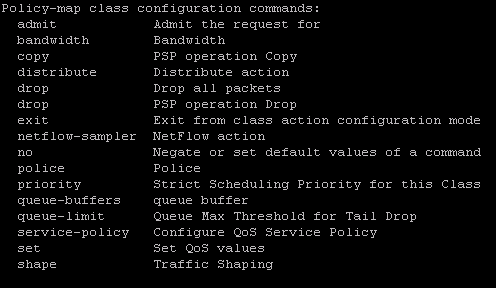
unfortunately not, cat3650/3850 just offers transmit as confirm action
@Joseph W. Doherty wrote:
If it doesn't work as desired, can you use an ingress policy to mark all traffic in that class to AF21, allowing the policer to down mark the overrate traffic?
I just added a second possibility to my initial post - do you mean this option? It is possible, but I'm also there not sure, if it work like this.
will queue limits applay, to differentiate between AF21, 22 and 23? (apparantly WRED is not available, so only tail drop is possible - isn't it?)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-18-2019 09:46 AM
What I was suggesting was in ingress policy to set all class AF2x to AF21, then allowing the egress policy to down mark if some traffic is overrate. I.e. I'm not sure whether traffic that conforms to the policer would get the AF21 marking.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-23-2019 02:46 AM
Hello,
thanks for answers, the solution was an update to version 16 (everest), there is possible to set "conform-action set-dscp-transmit <value>"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-23-2019 11:23 AM
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide