- Cisco Community
- Technology and Support
- Networking
- Wireless
- Re: AAA Authentication Failure for UserName
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 07:43 AM - edited 07-04-2021 12:28 AM
I recently tried to setup an CiscoWLC 4402 ios 7.0.235.0 with RADIUS on Win Serv 2008r2, I set up my security type as wpa2-ent aes encryption, Microsoft PEAP, and exported a certificate from my CA server, and installed on my client machine.
I am not sure what I am missing, let me know what information I need to further assist you. I attched some screenshots.
| 0 | Mon Jul 22 10:25:58 2013 | Client Excluded: MACAddress:8c:70:5a:d2:f6:f8 Base Radio MAC :00:1e:79:d6:25:e0 Slot: 0 User Name: unknown Ip Address: unknown Reason:802.1x Authentication failed 3 times. ReasonCode: 4 |
| 1 | Mon Jul 22 10:25:58 2013 | AAA Authentication Failure for UserName:host/106LPT073.itserve.com User Type: WLAN USER |
| 2 | Mon Jul 22 10:25:54 2013 | AAA Authentication Failure for UserName:host/106LPT073.itserve.com User Type: WLAN USER |
| 3 | Mon Jul 22 10:25:49 2013 | AAA Authentication Failure for UserName:host/106LPT073.itserve.com User Type: WLAN USER |
Solved! Go to Solution.
- Labels:
-
Wireless Security
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-23-2013 01:16 PM
The issue seems to be with server side certificate. Based on your very first post, I realise you're using a third party certificate. Is that possible that we issue a new certificate and try again. Or please export the certificate and attach it in your next reply.
Certificate Requirements for PEAP and EAP
http://technet.microsoft.com/en-us/library/a1ac8d7e-3479-46b4-932b-ab43362e021b
By default, these log files are located at %windir%\System32\Logfiles
http://technet.microsoft.com/en-us/library/dd197464%28v=ws.10%29.aspx
~BR
Jatin Katyal
**Do rate helpful posts**
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 07:51 AM
I reviewed the doc you attached. The WLAN config part looks fine. I'd like to know what error message are you seeing on the radius server under event viewer.
~BR
Jatin Katyal
**Do rate helpful posts**
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 07:55 AM
I have not seen any errors, only the information in the event viewer below
A LDAP connection with domain controller 106P101.itserve.com for domain ITSERVE is established.
Earlier this morning I was receiving, 2 hours ago. I fixed this already with the shared secret
An Access-Request message was received from RADIUS client 10.110.0.99 with a Message-Authenticator attribute that is not valid.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 08:05 AM
I'd like you to check under event viewer > custom views > server roles > Network policy and access services. Are we looking down in the same sections. In case there are no hits, please make sure the NPS service is running fine.
If all well, we may need to look at the radius/aaa debugs.
~BR
Jatin Katyal
**Do rate helpful posts**
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 08:15 AM
I attached both username and computer errors.
Network Policy Server denied access to a user.
Contact the Network Policy Server administrator for more information.
User:
Security ID: ITSERVE\ccampbell
Account Name: ITSERVE\ccampbell
Account Domain: ITSERVE
Fully Qualified Account Name: itserve.com/Accounts/Norcross/IT Staff/IT Administrators/Chad Campbell
Client Machine:
Security ID: NULL SID
Account Name: -
Fully Qualified Account Name: -
OS-Version: -
Called Station Identifier: 00-1e-79-d6-25-e0:ARCHWAY
Calling Station Identifier: 8c-70-5a-d2-f6-f8
NAS:
NAS IPv4 Address: 10.110.0.99
NAS IPv6 Address: -
NAS Identifier: WAP106-MM
NAS Port-Type: Wireless - IEEE 802.11
NAS Port: 29
RADIUS Client:
Client Friendly Name: Cisco WAP
Client IP Address: 10.110.0.99
Authentication Details:
Connection Request Policy Name: Secure Wireless Connections
Network Policy Name: Connections to other access servers
Authentication Provider: Windows
Authentication Server: 106P101.itserve.com
Authentication Type: EAP
EAP Type: -
Account Session Identifier: -
Logging Results: Accounting information was written to the local log file.
Reason Code: 65
Reason: The Network Access Permission setting in the dial-in properties of the user account in Active Directory is set to Deny access to the user. To change the Network Access Permission setting to either Allow access or Control access through NPS Network Policy, obtain the properties of the user account in Active Directory Users and Computers, click the Dial-in tab, and change Network Access Permission.
Computer
Network Policy Server denied access to a user.
Contact the Network Policy Server administrator for more information.
User:
Security ID: ITSERVE\106LPT073$
Account Name: host/106LPT073.itserve.com
Account Domain: ITSERVE
Fully Qualified Account Name: ITSERVE\106LPT073$
Client Machine:
Security ID: NULL SID
Account Name: -
Fully Qualified Account Name: -
OS-Version: -
Called Station Identifier: 00-1e-79-d6-25-e0:ARCHWAY
Calling Station Identifier: 8c-70-5a-d2-f6-f8
NAS:
NAS IPv4 Address: 10.110.0.99
NAS IPv6 Address: -
NAS Identifier: WAP106-MM
NAS Port-Type: Wireless - IEEE 802.11
NAS Port: 29
RADIUS Client:
Client Friendly Name: Cisco WAP
Client IP Address: 10.110.0.99
Authentication Details:
Connection Request Policy Name: Secure Wireless Connections
Network Policy Name: Secure Wireless Connections
Authentication Provider: Windows
Authentication Server: 106P101.itserve.com
Authentication Type: PEAP
EAP Type: -
Account Session Identifier: -
Logging Results: Accounting information was written to the local log file.
Reason Code: 23
Reason: An error occurred during the Network Policy Server use of the Extensible Authentication Protocol (EAP). Check EAP log files for EAP errors.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 08:21 AM
issue most likely with windows radius server... are you using ldap as identity base or radius server on windows?
from log seems eap handshake issue, as log stated you need to get eap log , or more effectively, go to microsoft/msdn for help.
Sent from Cisco Technical Support iPad App
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 08:22 AM
RADIUS.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 08:33 AM
The user request showing that it's hitting the wrong network access policy :
Network Policy Name: Connections to other access servers
However the machine authentication hitting the right one.
Let's do this
Go to network policies
Edit secure wireless connections.
Remove the condition "Machine Groups" equals ITSERVE\Wireless Users
save changes
Try again and check the error if you fail to connect. If we see eap failure we then need to look into eal log files.
~BR
Jatin Katyal
**Do rate helpful posts**
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 08:37 AM
I edited my dial in properties to allow it in AD, it was controlled by NPS policy previously, which was set to ignore.
I removed the machine groups condition, and now receive a different error.
Network Policy Server denied access to a user.
Contact the Network Policy Server administrator for more information.
User:
Security ID: ITSERVE\ccampbell
Account Name: ITSERVE\ccampbell
Account Domain: ITSERVE
Fully Qualified Account Name: itserve.com/Accounts/Norcross/IT Staff/IT Administrators/Chad Campbell
Client Machine:
Security ID: NULL SID
Account Name: -
Fully Qualified Account Name: -
OS-Version: -
Called Station Identifier: 00-1e-79-d6-25-e0:ARCHWAY
Calling Station Identifier: 8c-70-5a-d2-f6-f8
NAS:
NAS IPv4 Address: 10.110.0.99
NAS IPv6 Address: -
NAS Identifier: WAP106-MM
NAS Port-Type: Wireless - IEEE 802.11
NAS Port: 29
RADIUS Client:
Client Friendly Name: Cisco WAP
Client IP Address: 10.110.0.99
Authentication Details:
Connection Request Policy Name: Secure Wireless Connections
Network Policy Name: Connections to other access servers
Authentication Provider: Windows
Authentication Server: 106P101.itserve.com
Authentication Type: EAP
EAP Type: -
Account Session Identifier: -
Logging Results: Accounting information was written to the local log file.
Reason Code: 66
Reason: The user attempted to use an authentication method that is not enabled on the matching network policy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 08:41 AM
You need to select the authentication peap under the "secure wireless connection" network policies. Please refer the screen shot attached.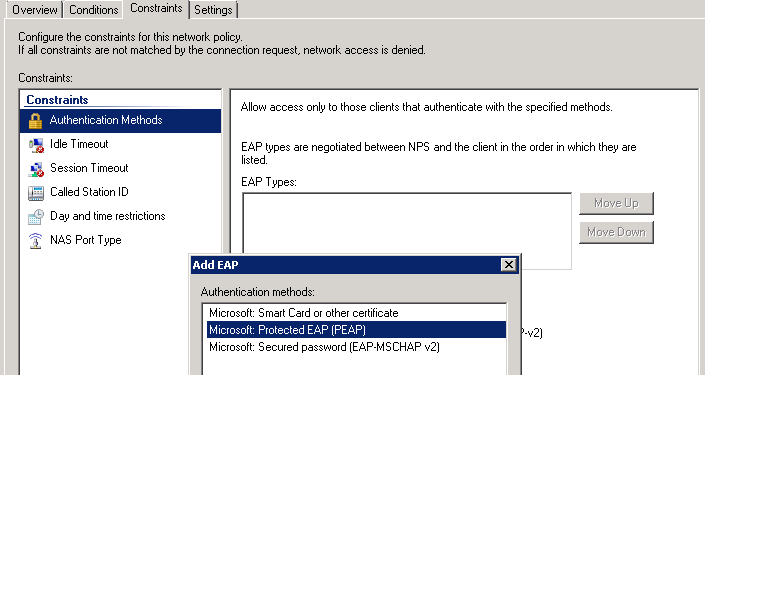
Save the changes and try again. Let me know if you see any more errors.
~BR
Jatin Katyal
**Do rate helpful posts**
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 08:50 AM
Jatin I already have it set.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 08:53 AM
Not sure if this is related?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2013 09:38 AM
Yup, you have it configured however the request is still going to some other policy where it's not checked.
Network Policy Name: Connections to other access servers
You may try this, go to the policy"secure wireless connection" network policiy and add a condition
NAS IPv4 address equals 10.110.0.99
This should work fine.
~BR
Jatin Katyal
**Do rate helpful posts**
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-23-2013 04:36 AM
Still did not work, I am thinking the issue is with the certificate just want to verify it,
I keep receiving the below error, where can I find the log file if it is not in C:\Windows\System32\Logfiles
An error occurred during the Network Policy Server use of the Extensible Authentication Protocol (EAP). Check EAP log files for EAP errors.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-23-2013 01:16 PM
The issue seems to be with server side certificate. Based on your very first post, I realise you're using a third party certificate. Is that possible that we issue a new certificate and try again. Or please export the certificate and attach it in your next reply.
Certificate Requirements for PEAP and EAP
http://technet.microsoft.com/en-us/library/a1ac8d7e-3479-46b4-932b-ab43362e021b
By default, these log files are located at %windir%\System32\Logfiles
http://technet.microsoft.com/en-us/library/dd197464%28v=ws.10%29.aspx
~BR
Jatin Katyal
**Do rate helpful posts**
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide
