- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless
- CAPWAP AP 802.1x supplicant with EAP-TLS
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
CAPWAP AP 802.1x supplicant with EAP-TLS
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-28-2020 01:34 PM - edited 07-05-2021 11:36 AM
Hello Community!
We have a highly secure environment with NAC on switchports. We need APs to use pre-provisioned(during staging) LSC certificates (same for DTLS encryption and AP Auth on the WLC) during 802.1x EAP-TLS authentication on the NAC switchports. We had already chained WLC with root CA and provisioned LSC certs to all APs as "802.1x + CAPWAP-DTLS". APs are using LSC certs for both CAPWAP Data and Control DTLS encryption. NAC is not enabled on the switch ports to which APs are connected yet.
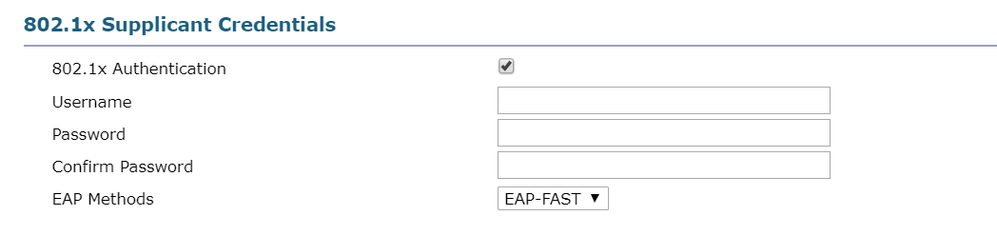
The issue is when we try enable "802.1x Authentication" in "802.1x Supplicant Credentials" as EAP-TLS in Access Points Global configuration in GUI, the WLC asking for username and password. (The picture is from the configuration guide).
That's confusing, since we intend to use EAP-TLS which require certificate instead of credentials. Configuration guides referred to this feature says: "Also configure user name and password."
What will those username/password be?
Thanks!
- Labels:
-
Wireless Security
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-28-2020 01:59 PM
Depending on what WLC version you are running the only 802.1x auth for the AP to the network is EAP-FAST.
From
Prior to rel 8.7, AP port 802.1x only supported EAP-FAST, in rel 8.7 the AP supplicant will also support EAP-TLS / EAP-PEAP
*** Please rate helpful posts ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-29-2020 12:48 AM
Thanks for you reply!
It's 8.10.105, so this feature is supported, and we have an option to choose EAP-TLS as authentication method. We just still being asked for a username and password when we choose it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-03-2020 09:34 AM
Any ideas?
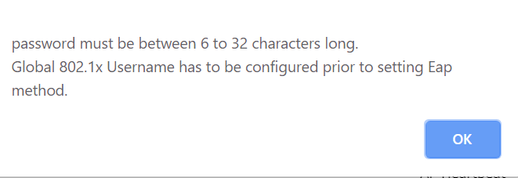
When I try to enable 802.1x Authentication:
I get this error:
What's Global 802.1x Username? I want to use EAP-TLS...
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-06-2020 02:51 PM
Hello Murinos,
Did you figure out how to solve this ? If you configure EAP-TLS without any username/password set, is it working ?
AL
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-08-2020 02:23 AM
Hello aleopoldie,
No, we bumped to another problem. The ISE we use as AAA server for NAC can't trust the Root CA we use for SCEP on WLC. So, it will not accept certificates we issue for APs for EAP-TLS.
We are bound with EAP-FAST (login/pass) and mac check.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-14-2022 02:28 AM - edited 01-14-2022 02:39 AM
Bump ? - Any news on this , we are all holding our collective breaths in anticipation
/Thomas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-10-2022 04:39 AM
Unfortunately, no.
We were not allowed to power on 'main' root CA which is used for all production networking infrastructure. The 'additional' root CA which is used for SCEP on WLC and APs cant' be made trusted on ISE. ISE can trust only single root CA (2 years ago). So it could not auntheticate AP's certificates issued by 'additional' root CA on NAC port.
The task is done and we left the site, so it's final.
If only ISE could support several root CA's that time, then it could be possible to meke everything right.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-22-2022 03:46 PM
Hello @Murinos
I am looking at deploying EAP-TLS to a bunch of AireOS WAPs and I came across this thread. What do you mean by "ISE can only trust single root CA" ?
ISE can have many different Trusted CA certs installed, for the purpose of checking the CLIENT certificate.
What you are alluding to, is the fact that ISE only supports one EAP System certificate. This is still a limitation. But it's not a problem for clients who don't check the Authenticating Server's (RADIUS server's) certificate. e.g. In Windows supplicants you can turn that validation off.
Anyway. Back to Cisco WAPs and EAP-TLS. Your ISE PSN's should have their EAP System cert issued by the corporate PKI. But as far as the clients is concerned, they can have their certs issued by multiple different CA - as long as ISE has those CA certs installed under Trusted Certs, and the usage is ticked for "Client authentication".
Are you 100% sure that the Cisco WAP expects to always see the ISE EAP cert signed by the same cert that signed the WAP cert? That would be weird.
I am still trying to figure out how to get PKI certs onto a Cisco AireOS WAP without using SCEP. I just want to install the cert manually.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide