- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless
- Re: Inter-Release Controller Mobility (IRCM) with 5508 Fail : Contro
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-16-2021 05:05 AM - edited 07-05-2021 01:01 PM
Hi all
Device info as below:
WLC-5508 controller running 8.5.164.216
WLC-9800 controller running 17.3.2a
The situation:
After config the mobility setting ; the status displayed is :Control Path Down
From the WLC-9800 show logg , found that the WLC-5508's MIC is expired:
Jan 16 12:40:22.264: %DTLS_TRACE_MSG-3-WLC_DTLS_ERR: Chassis 2 R0/0: mobilityd: DTLS Error, session:10.36.197.177[16666], Certificate validation failed
Jan 16 12:40:52.263: %PKI-3-CERTIFICATE_INVALID_EXPIRED: Certificate chain validation has failed. The certificate (SN: 16D8553C000000119DEC) has expired. Validity period ended on 2020-11-23T17:58:29Z
Jan 16 12:40:52.265: %CERT_MGR_ERRMSG-3-CERT_VALIDATION_ERR: Chassis 2 R0/0: mobilityd: Certificate Validation Error, Cert validation status:pki_ssl_status@pki_ssl_status:PKI_SSL_ERROR
Is there any way to let WLC-9800 ignore the MIC expired ?
I have already excute the command on the WLC-5508 : config ap cert-expiry-ignore mic enable
--------------------------------------------------------------------------
Other information:
WLC-5508
(TPE-WLC-5508-6) >show mobility summary encryption
Mobility Number of Mobility members configure.... 2
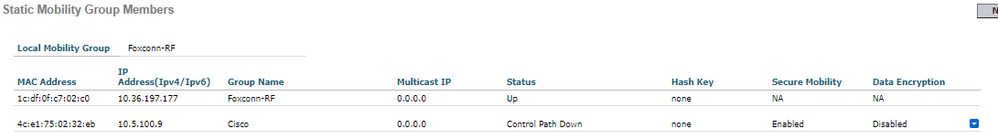
MAC Address IP Address Group Name Secure Data Encryption Status
1c:df:0f:c7:02:c0 10.36.197.177 Foxconn-RF N/A N/A Up
4c:e1:75:02:32:eb 10.5.100.9 Cisco Enabled Disabled Control Path Down
(TPE-WLC-5508-6) >show mobility summary
Mobility Protocol Port........................... 16666
Default Mobility Domain.......................... Foxconn-RF
Multicast Mode .................................. Disabled
Mobility Domain ID for 802.11r................... 0xd58a
Mobility Keepalive Interval...................... 10
Mobility Keepalive Count......................... 3
Mobility Group Members Configured................ 2
Mobility Control Message DSCP Value.............. 48
Controllers configured in the Mobility Group
MAC Address IP Address Group Name Multicast IP Status
1c:df:0f:c7:02:c0 10.36.197.177 Foxconn-RF 0.0.0.0 Up
4c:e1:75:02:32:eb 10.5.100.9 Cisco 0.0.0.0 Control Path Down
WLC-9800
WLC01-C9800-40#show wireless management trustpoint
Trustpoint Name : CISCO_IDEVID_SUDI
Certificate Info : Available
Certificate Type : MIC
Certificate Hash : 585d9f405a1cf79f7c5cf752a1eb0bec33874d1f
Private key Info : Available
FIPS suitability : Not Applicable
!
WLC01-C9800-40#show wireless mobilit summary
Mobility Summary
Wireless Management VLAN: 100
Wireless Management IP Address: 10.5.100.9
Wireless Management IPv6 Address:
Mobility Control Message DSCP Value: 48
Mobility Keepalive Interval/Count: 10/3
Mobility Group Name: Cisco
Mobility Multicast Ipv4 address: 0.0.0.0
Mobility Multicast Ipv6 address: ::
Mobility MAC Address: 4ce1.7502.32eb
Mobility Domain Identifier: 0xdc29
Controllers configured in the Mobility Domain:
IP Public Ip MAC Address Group Name Multicast IPv4 Multicast IPv6 Status PMTU
------------------ ------------------------------------------------------------------------------
10.5.100.9 N/A 4ce1.7502.32eb Cisco 0.0.0.0 :: N/A N/A
10.36.197.177 10.36.197.177 1cdf.0fc7.02c0 Foxconn-RF 0.0.0.0 :: Control Path Down 1385
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-17-2021 07:16 PM
OK, here is the thing, the cli command you have (config ap cert-expiry-ignore mic enable) will work only on AireOS WLCs, meaning this will work between the AireOS WLC and APs and between AireOS WLC and other AireOS WLC when forming mobility.
In this case you want to do mobility between AireOS and 9800, but the 9800 is complaining about the AireOS cert because it is expired, what you need to do is to configure the 9800 to allow expired certificate, this is documented in details here in this bug CSCvr03489: Need CLI knob to ignore MIC expiration on 9800 https://bst.cloudapps.cisco.com/bugsearch/bug/CSCvr03489 and also documented in the 9800 config guide, here are the steps:
9800-1#conf t
9800-1(config)#crypto pki certificate map map1 1
9800-1(ca-certificate-map)#issuer-name co Cisco Manufacturing CA
9800-1(ca-certificate-map)#exit
9800-1(config)#crypto pki trustpool policy
9800-1(ca-trustpool)#match certificate map1 allow expired-certificate
9800-1(ca-trustpool)#end
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-16-2021 05:45 AM
@Bill lo wrote:
WLC-5508 controller running 8.5.164.216
Go back to TAC because the WLC is running a special engineering release. Only TAC will know how these specially released software behaves.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-18-2021 09:58 AM
@Leo Laohoo8.5.164.216 is actually a published release now, with release notes:
https://software.cisco.com/download/home/282600534/type/280926587/release/8.5IRCM
https://www.cisco.com/c/en/us/td/docs/wireless/controller/release/notes/crn85mr6_ircm.html
Interestingly https://www.cisco.com/c/en/us/support/docs/wireless/wireless-lan-controller-software/200046-tac-recommended-aireos.html#anc10 hasn't been updated to include that yet ... @Grendizer ?
Please click Helpful if this post helped you and Select as Solution (drop down menu at top right of this reply) if this answered your query.
------------------------------
TAC recommended codes for AireOS WLC's and TAC recommended codes for 9800 WLC's
Best Practices for AireOS WLC's, Best Practices for 9800 WLC's and Cisco Wireless compatibility matrix
Check your 9800 WLC config with Wireless Config Analyzer using "show tech wireless" output or "config paging disable" then "show run-config" output on AireOS and use Wireless Debug Analyzer to analyze your WLC client debugs
Field Notice: FN63942 APs and WLCs Fail to Create CAPWAP Connections Due to Certificate Expiration
Field Notice: FN72424 Later Versions of WiFi 6 APs Fail to Join WLC - Software Upgrade Required
Field Notice: FN72524 IOS APs stuck in downloading state after 4 Dec 2022 due to Certificate Expired
- Fixed in 8.10.196.0, latest 9800 releases, 8.5.182.12 (8.5.182.13 for 3504) and 8.5.182.109 (IRCM, 8.5.182.111 for 3504)
Field Notice: FN70479 AP Fails to Join or Joins with 1 Radio due to Country Mismatch, RMA needed
How to avoid boot loop due to corrupted image on Wave 2 and Catalyst 11ax Access Points (CSCvx32806)
Field Notice: FN74035 - Wave2 APs DFS May Not Detect Radar After Channel Availability Check Time
Leo's list of bugs affecting 2800/3800/4800/1560 APs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-18-2021 12:39 PM
Yes because in general for any new image “even if it has a lot of bug fixes” the Wireless team need to wait some time before promoting that image to a possible recommended release, they can’t do that yet with this image because it is still relatively new.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-18-2021 02:41 PM
@Rich R wrote:
@Leo Laohoo8.5.164.216 is actually a published release now, with release notes:
Nuts. WNBU has re-spun the IRCM image to a Special Engineering Release.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-16-2021 08:45 AM
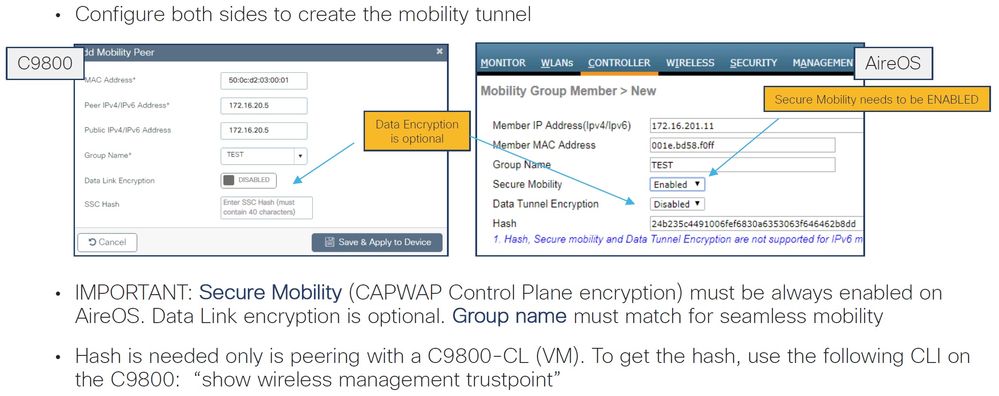
Secure Mobility on the 5508 is disabled, this need to be enabled, check the attached as a reference.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-16-2021 08:24 PM
Hi Grendizer
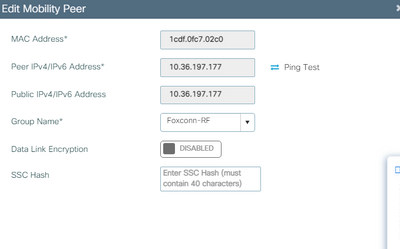
Secure Mobility on the 5508 is enable:
note: the C9800 use MIC not SSC : the Hash is no needed
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-17-2021 07:16 PM
OK, here is the thing, the cli command you have (config ap cert-expiry-ignore mic enable) will work only on AireOS WLCs, meaning this will work between the AireOS WLC and APs and between AireOS WLC and other AireOS WLC when forming mobility.
In this case you want to do mobility between AireOS and 9800, but the 9800 is complaining about the AireOS cert because it is expired, what you need to do is to configure the 9800 to allow expired certificate, this is documented in details here in this bug CSCvr03489: Need CLI knob to ignore MIC expiration on 9800 https://bst.cloudapps.cisco.com/bugsearch/bug/CSCvr03489 and also documented in the 9800 config guide, here are the steps:
9800-1#conf t
9800-1(config)#crypto pki certificate map map1 1
9800-1(ca-certificate-map)#issuer-name co Cisco Manufacturing CA
9800-1(ca-certificate-map)#exit
9800-1(config)#crypto pki trustpool policy
9800-1(ca-trustpool)#match certificate map1 allow expired-certificate
9800-1(ca-trustpool)#end
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-18-2021 05:39 AM
Hi Grendizer
Perfect:
Thanks a lot!!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-14-2023 05:57 AM
I have a similar issue, but above configuration didn't work
#sh crypto pki trustpool policy
Trustpool Policy
Chain validation will stop at the first CA certificate in the pool
Trustpool CA certificates will expire 21:25:42 UTC May 14 2029
Trustpool revocation checking is disabled:
Certificate matching is disabled
Policy Overrides:
map: map1
match: issuer-name co cisco manufacturing ca
action: allow expired certificates
Wireless Management VLAN: 1500
Wireless Management IP Address: 10.5.4.250
Wireless Management IPv6 Address:
Mobility Control Message DSCP Value: 48
Mobility High Cipher : False
Mobility DTLS Supported Ciphers: TLS_ECDHE_RSA_AES128_GCM_SHA256, TLS_RSA_AES256_GCM_SHA384, TLS_RSA_AES128_CBC_SHA
Mobility Keepalive Interval/Count: 10/3
Mobility Group Name: 45PL
Mobility Multicast Ipv4 address: 0.0.0.0
Mobility Multicast Ipv6 address: ::
Mobility MAC Address: c44d.84c6.e08b
Mobility Domain Identifier: 0x9df
Controllers configured in the Mobility Domain:
IP Public Ip MAC Address Group Name Multicast IPv4 Multicast IPv6 Status PMTU
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
10.16.4.250 N/A c44d.84c6.e08b 45PL 0.0.0.0 :: N/A N/A
10.4.6.1 10.4.6.1 f866.f2fa.2340 45PL 0.0.0.0 :: Control And Data Path Down 1385
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-14-2023 06:48 AM
Your config does not look the same as what @Grendizer recommended:
> 9800-1(ca-certificate-map)#issuer-name co Cisco Manufacturing CA
match: issuer-name co cisco manufacturing ca
So step number 1: configure as recommended.
Please click Helpful if this post helped you and Select as Solution (drop down menu at top right of this reply) if this answered your query.
------------------------------
TAC recommended codes for AireOS WLC's and TAC recommended codes for 9800 WLC's
Best Practices for AireOS WLC's, Best Practices for 9800 WLC's and Cisco Wireless compatibility matrix
Check your 9800 WLC config with Wireless Config Analyzer using "show tech wireless" output or "config paging disable" then "show run-config" output on AireOS and use Wireless Debug Analyzer to analyze your WLC client debugs
Field Notice: FN63942 APs and WLCs Fail to Create CAPWAP Connections Due to Certificate Expiration
Field Notice: FN72424 Later Versions of WiFi 6 APs Fail to Join WLC - Software Upgrade Required
Field Notice: FN72524 IOS APs stuck in downloading state after 4 Dec 2022 due to Certificate Expired
- Fixed in 8.10.196.0, latest 9800 releases, 8.5.182.12 (8.5.182.13 for 3504) and 8.5.182.109 (IRCM, 8.5.182.111 for 3504)
Field Notice: FN70479 AP Fails to Join or Joins with 1 Radio due to Country Mismatch, RMA needed
How to avoid boot loop due to corrupted image on Wave 2 and Catalyst 11ax Access Points (CSCvx32806)
Field Notice: FN74035 - Wave2 APs DFS May Not Detect Radar After Channel Availability Check Time
Leo's list of bugs affecting 2800/3800/4800/1560 APs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-14-2023 07:03 AM
I have entered the command same as issuer-name co Cisco Manufacturing CA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-14-2023 07:04 AM
but when i enter the sh command it will appear cisco manufacturing ca
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-14-2023 07:15 AM
Ok interesting!
What version of software on 5508?
What version of software on 9800?
Please click Helpful if this post helped you and Select as Solution (drop down menu at top right of this reply) if this answered your query.
------------------------------
TAC recommended codes for AireOS WLC's and TAC recommended codes for 9800 WLC's
Best Practices for AireOS WLC's, Best Practices for 9800 WLC's and Cisco Wireless compatibility matrix
Check your 9800 WLC config with Wireless Config Analyzer using "show tech wireless" output or "config paging disable" then "show run-config" output on AireOS and use Wireless Debug Analyzer to analyze your WLC client debugs
Field Notice: FN63942 APs and WLCs Fail to Create CAPWAP Connections Due to Certificate Expiration
Field Notice: FN72424 Later Versions of WiFi 6 APs Fail to Join WLC - Software Upgrade Required
Field Notice: FN72524 IOS APs stuck in downloading state after 4 Dec 2022 due to Certificate Expired
- Fixed in 8.10.196.0, latest 9800 releases, 8.5.182.12 (8.5.182.13 for 3504) and 8.5.182.109 (IRCM, 8.5.182.111 for 3504)
Field Notice: FN70479 AP Fails to Join or Joins with 1 Radio due to Country Mismatch, RMA needed
How to avoid boot loop due to corrupted image on Wave 2 and Catalyst 11ax Access Points (CSCvx32806)
Field Notice: FN74035 - Wave2 APs DFS May Not Detect Radar After Channel Availability Check Time
Leo's list of bugs affecting 2800/3800/4800/1560 APs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-14-2023 07:16 AM
this is the logs i can see on 9800
%MM_INFRA_LOG-3-MSG_PROC_FAILED: Chassis 1 R0/0: mobilityd: 0000.0000.0000: Unable to process the received mobility message unknown from ipv4: 10.4.6.1 . reason: Unable to parse the msg
Dec 14 13:05:47.955: %MM_INFRA_LOG-3-MSG_PROC_FAILED: Chassis 1 R0/0: mobilityd: 0000.0000.0000: Unable to process the received mobility message unknown from ipv4: 10.4.6.1 . reason: Unable to parse the msg
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide