- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless
- Re: ISE 2.4 and 9800 WLC: Wireless guest issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-12-2021 01:25 AM - edited 09-21-2021 02:47 AM
Hello Experts,
I am facing a issue with guest access authentication. Old AIROS wlcs are working but now I have a installed a new 9800 wlc and its creating an issue.
Requesting help to troubleshoot below authentication fail error messages seen for wireless guest users.
| Event | 5400 Authentication failed |
| Failure Reason | 15039 Rejected per authorization profile |
| Resolution | Authorization Profile with ACCESS_REJECT attribute was selected as a result of the matching authorization rule. Check the appropriate Authorization policy rule-results. |
| Root cause | Selected Authorization Profile contains ACCESS_REJECT attribute |
| Username | USERNAME |
Its not hitting the right Authentication policy.
Auth policies:
Steps
| 11001 | Received RADIUS Access-Request | |
| 11017 | RADIUS created a new session | |
| 15049 | Evaluating Policy Group | |
| 15008 | Evaluating Service Selection Policy | |
| 15048 | Queried PIP | |
| 15041 | Evaluating Identity Policy | |
| 15013 | Selected Identity Source - | |
| 22043 | Current Identity Store does not support the authentication method; Skipping it | |
| 22064 | Authentication method is not supported by any applicable identity store(s) | |
| 22058 | The advanced option that is configured for an unknown user is used | |
| 22060 | The 'Continue' advanced option is configured in case of a failed authentication request | |
| 24715 | ISE has not confirmed locally previous successful machine authentication for user in Active Directory | |
| 15036 | Evaluating Authorization Policy | |
| 15048 | Queried PIP | |
| 15048 | Queried PIP | |
| 15048 | Queried PIP | |
| 15016 | Selected Authorization Profile - DenyAccess | |
| 15039 | Rejected per authorization profile | |
| 11003 | Returned RADIUS Access-Reject | |
| 5434 | Endpoint conducted several failed authentications of the same scenario |
Thanks in advance
Best Regards
Solved! Go to Solution.
- Labels:
-
Wireless LAN Controller
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-18-2021 08:58 AM - edited 08-18-2021 09:00 AM
Just remove the below lines as I mentioned before:
redirect on-success https://www.grammer.com/
redirect portal ipv4 192.0.2.1
with the above, this will be sent to ISE as Login, meaning to match on ISE you need Radius:Service-Type = Login
this is used if you have a Web server that provide you a portal or if you want to use one of the ISE portals, usually a copy of the sponsored Guest Portal, so in your case because you want to use the 9800 customized portal then you have to leave those fields empty by removing the above cli lines and that's mean when you check the username/pass with ISE (using ISE locally defined users or from Active Directory) then the 9800 will send those as "Outbound", Radius:Service-Type = Outbound
One more thing, in your ISE Policy Set, you're not telling ISE where to look and check for the usernames/pass that Guests will be using, meaning, if you need to check against AD group then you specify that group, if you need to check them against ISE local group you need to specify that. In below screenshot you can see that I'm using simple policy set to check both AD and internal ISE group without checking the service type, but you can definitely use that check too.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2021 01:45 AM
Check this link:
https://thewlan.com.au/2020/07/14/9800-local-webauth-certs/
Regards
Dont forget to rate helpful posts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-21-2021 01:30 AM
You can try this method as well.. I tried in my lab and it worked:
First you need to create a trustpoint on the WLC. The trustpoint contains the certificate authority that signed the certificate in use.
WLC1 (config)#crypto pki trustpoint WILDCARD
WLC1 (ca-trustpoint)#fqdn *.xyz.com
WLC1 (ca-trustpoint)#subject-name cn=*.xyz.com
WLC1 (ca-trustpoint)#revocation-check crl
WLC1 (ca-trustpoint)#rsakeypair WILDCARD
Next, you should import the certificate. There are multiple ways for importing the certificate, but you can use FTP/tftp to transfer the certificate from your laptop to the wlc.
Info: Certificate must be in PKCS12 (.pfx) form
WLC1(config)#crypto pki import WILDCARD pkcs12 ftp: password xyz12345
% Importing pkcs12...
Address or name of remote host []? 192.168.21.25
Source filename [WILDCARD]? WildcardCert.pfx
Reading file from ftp://192.168.21.25/WildcardCert.pfx!
[OK - 6048/4096 bytes]
% The CA cert is not self-signed.
% Do you also want to create trustpoints for CAs higher in
% the hierarchy? [yes/no]:yes
*Sep 16 10:38:02 UTC: %CRYPTO_ENGINE-5-KEY_ADDITION: A key named WILDCARD has been generated or imported by pki-pkcs12
CRYPTO_PKI: Imported PKCS12 file successfully.
WLC1(config)#exit
WLC1(config)#wr
*Sep 16 10:38:06 UTC: %PKI-6-TRUSTPOINT_CREATE: Trustpoint: WILDCARD-rrr1 created succesfully
*Sep 16 10:38:06 UTC: %PKI-6-PKCS12_IMPORT_SUCCESS: PKCS #12 import in to trustpoint WILDCARD successfully imported.
The certificate is now successfully imported into the WLC and can be associated with the Webauth wlan.
then you can assign wildcard certificate to webauth parameter map.
Regards
Dont forget to arte helpful posts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-12-2021 03:29 PM
15039 Rejected per authorization profile
Can you show the full failure log, please?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2021 12:50 AM
which logs you want to me paste ?
from ISE side or debug from WLC ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-16-2021 10:47 AM
you need to change (redirect portal ipv4 192.0.2.1) to the ISE IP Address instead.
Check this line (redirect for-login guest.corp.com) Which ISE portal will reply the requests?
you're using Guest Users (meaning the users are configured in ISE)
not sure about this condition: WLC_Web_Authentication (it needs to check ISE Guest Users group as you specified in AuthC rule)
moreover, ISE portal is using by default TCP port 8443 and with that you will need to create a Pre-Auth ACL that will be applied on the WLAN > Security > Layer3 > Preauthentication ACL > IPv4, example ACL below:
permit tcp any host ISE_IP_ADDRESS eq 8443
permit tcp host ISE_IP_ADDRESS eq 8443 any
permit tcp any any eq domain
permit udp any any eq domain
permit udp any any eq bootpc
permit udp any any eq bootps
deny ip any any
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-16-2021 10:10 PM
Hi,
Thanks for your input but I am using Portal on customized WLC itself.
Portal is on WLC
Guest users are in ISE sponsor Portal
Best Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-17-2021 09:58 AM - edited 08-17-2021 10:02 AM
Ok, then you need to do these changes:
Changes on 9800:
Add the below command:
aaa authentication webauth default local group ISE
to check the WLC local users first then ISE, if you need to check the 9800 local users/guest accounts then you have to add this line too (aaa authorization network default local)
OR
aaa authentication webauth default group ISE
to check the users from ISE only
Note: "Named Method lists not supported for webauth" so in your case we can't use the method list ISE so instead we have to use default as in above cli.
also you shouldn't use the below lines under global parameter map: (by the way you can use different "new" parameter map and will work too, meaning doesn't have to be the global parameter map but that works too)
redirect for-login guest.corp.com
redirect portal ipv4 192.0.2.1
Because if you want to use guest.corp.com as the DNS name to the ipv4 virtual IP address then you need to put that in (Virtual IPv4 Hostname) section also you need a DNS record to point the guests to the 9800 virtual IP address, meaning, DNS record for guest.corp.com=192.0.2.1 and of course you need a certificate signed by public CA (with SAN) so guests will not see certificate error, info is here https://www.cisco.com/c/en/us/support/docs/wireless/catalyst-9800-series-wireless-controllers/213917-generate-csr-for-third-party-certificate.html
side note: i didn't see ISE1 as RADIUS configured but it used under group ISE so either you configure that or remove it from that group
for more info, check this doc Custom Web Authentication on Catalyst 9800 Wireless Controllers Configuration Example
https://www.cisco.com/c/en/us/support/docs/wireless/catalyst-9800-series-wireless-controllers/216121-custom-web-authentication-on-catalyst-98.html
Changes on ISE:
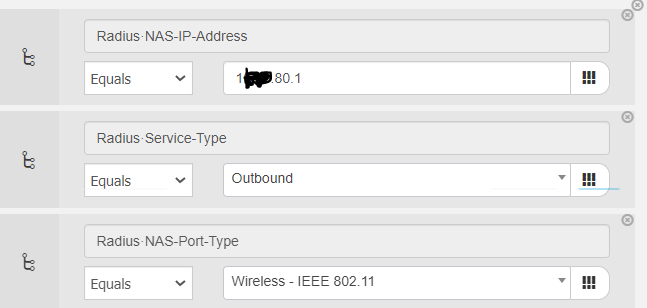
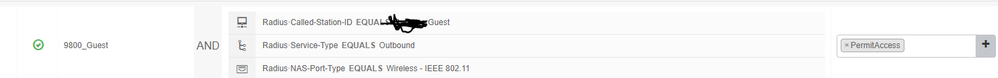
You're using (WLC_Web_Authentication) as a condition, the rules for this condition are:
Radius:NAS-Port-Type = Wireless - IEEE 802.11
Radius:Service-Type = Login
while in this case the Service Type is "Outbound" so will not match your rule, so you need to remove that condition or create a new one with Radius:Service-Type = Outbound
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-18-2021 01:13 AM - edited 09-21-2021 02:49 AM
Hi @Grendizer ,
Thanks for detailed explanation!
I did as you mentioned above but still hitting the default policy with Deny Access:
1. Method list name created with name "default"
aaa authentication login default local group ISE
aaa authentication webauth default local group ISE
2. New Parameter MAP:
parameter-map type webauth LWA
type webauth
sleeping-client
redirect portal ipv4 192.0.2.1
logout-window-disabled
success-window-disable
cisco-logo-disable
3. Changes on ISE:
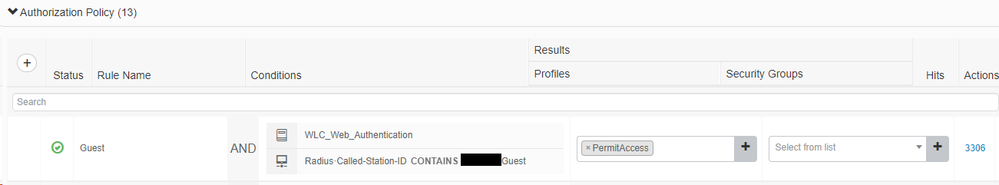
Authentication
AuthZ
SSId Config:
wlan CorpGuest 1 CorpGuest
peer-blocking drop
no security wpa
no security wpa wpa2
no security wpa wpa2 ciphers aes
no security wpa akm dot1x
security web-auth
security web-auth authentication-list default
security web-auth parameter-map LWA
no shutdown
Bets Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-18-2021 08:58 AM - edited 08-18-2021 09:00 AM
Just remove the below lines as I mentioned before:
redirect on-success https://www.grammer.com/
redirect portal ipv4 192.0.2.1
with the above, this will be sent to ISE as Login, meaning to match on ISE you need Radius:Service-Type = Login
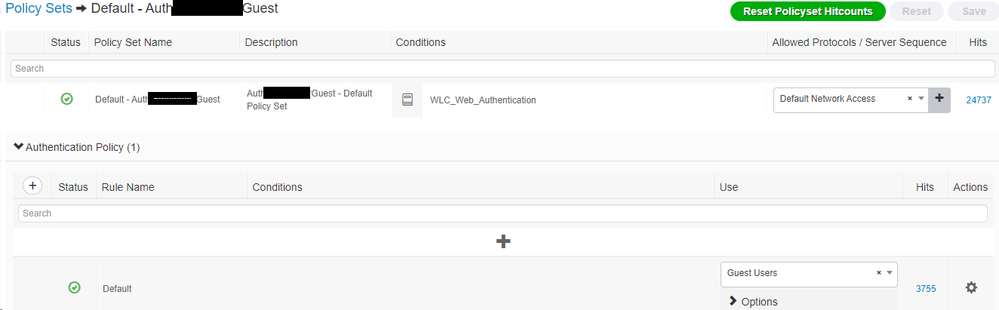
this is used if you have a Web server that provide you a portal or if you want to use one of the ISE portals, usually a copy of the sponsored Guest Portal, so in your case because you want to use the 9800 customized portal then you have to leave those fields empty by removing the above cli lines and that's mean when you check the username/pass with ISE (using ISE locally defined users or from Active Directory) then the 9800 will send those as "Outbound", Radius:Service-Type = Outbound
One more thing, in your ISE Policy Set, you're not telling ISE where to look and check for the usernames/pass that Guests will be using, meaning, if you need to check against AD group then you specify that group, if you need to check them against ISE local group you need to specify that. In below screenshot you can see that I'm using simple policy set to check both AD and internal ISE group without checking the service type, but you can definitely use that check too.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-18-2021 10:06 PM
Thanks, I will configure the policies as you mentioned and will give a try and let you know!
Best Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2021 12:22 AM
Thank you. It working now.
Could you please also tell me how to install a wildcard certificate for webauth certificate eon 9800 WLC?
Thanks in advance.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2021 01:45 AM
Check this link:
https://thewlan.com.au/2020/07/14/9800-local-webauth-certs/
Regards
Dont forget to rate helpful posts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-13-2021 07:59 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-14-2021 04:29 AM
I will try to install it and let you know.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-21-2021 01:30 AM
You can try this method as well.. I tried in my lab and it worked:
First you need to create a trustpoint on the WLC. The trustpoint contains the certificate authority that signed the certificate in use.
WLC1 (config)#crypto pki trustpoint WILDCARD
WLC1 (ca-trustpoint)#fqdn *.xyz.com
WLC1 (ca-trustpoint)#subject-name cn=*.xyz.com
WLC1 (ca-trustpoint)#revocation-check crl
WLC1 (ca-trustpoint)#rsakeypair WILDCARD
Next, you should import the certificate. There are multiple ways for importing the certificate, but you can use FTP/tftp to transfer the certificate from your laptop to the wlc.
Info: Certificate must be in PKCS12 (.pfx) form
WLC1(config)#crypto pki import WILDCARD pkcs12 ftp: password xyz12345
% Importing pkcs12...
Address or name of remote host []? 192.168.21.25
Source filename [WILDCARD]? WildcardCert.pfx
Reading file from ftp://192.168.21.25/WildcardCert.pfx!
[OK - 6048/4096 bytes]
% The CA cert is not self-signed.
% Do you also want to create trustpoints for CAs higher in
% the hierarchy? [yes/no]:yes
*Sep 16 10:38:02 UTC: %CRYPTO_ENGINE-5-KEY_ADDITION: A key named WILDCARD has been generated or imported by pki-pkcs12
CRYPTO_PKI: Imported PKCS12 file successfully.
WLC1(config)#exit
WLC1(config)#wr
*Sep 16 10:38:06 UTC: %PKI-6-TRUSTPOINT_CREATE: Trustpoint: WILDCARD-rrr1 created succesfully
*Sep 16 10:38:06 UTC: %PKI-6-PKCS12_IMPORT_SUCCESS: PKCS #12 import in to trustpoint WILDCARD successfully imported.
The certificate is now successfully imported into the WLC and can be associated with the Webauth wlan.
then you can assign wildcard certificate to webauth parameter map.
Regards
Dont forget to arte helpful posts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-21-2021 01:34 AM
Thank you I will try it!
Could @Grendizer @Sandeep Choudhary please help me about this issue ? Here is the post about my Mobility express issue:
Thanks again
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide