- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless
- Re:OfficeExtend in a dual Firewalled DMZ - OEAP not registering
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2013 09:13 AM - edited 07-04-2021 01:23 AM
Hello!
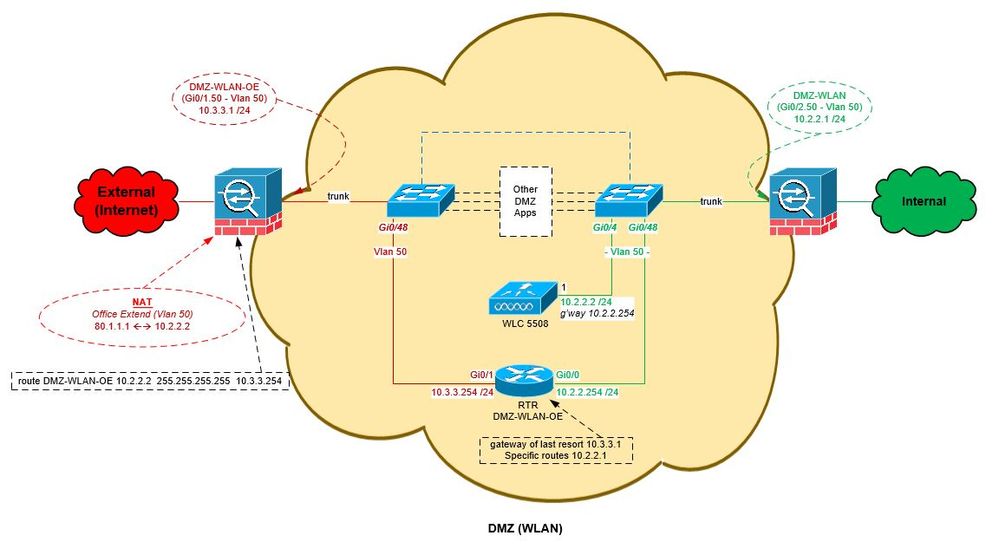
Just wondering if it's possible to configure a DMZ WLC in such a way that it will accept a join request from an OEAP on a none-management (outside) interface? (Port
As you can see from the attached diagram I’m trying to use the DMZ WLC as a physical separator between good and evil, however it appears that the OEAP is unable to join the WLC unless it’s join request is heard on the management interface (Port 1) ...unfortunately for me this is an inside interface and in order to allow this to happen I would have to allow the outside join request to pass between the outside and inside switches which isn’t exactly what I want – In saying that this is possible as we do have a trunk link (for management) in place between the switches however I would prefer not to.
You’ll see that NATing on the outside Firewall is working and the join request is hitting the OE interface (Port 8), however it’s rejecting it due to it not being a management interface, this is regardless of Port 8 being set up as a Dynamic AP Management interface or not. I have tried finding out why this is happening however some forum posts suggest that the join request has to be heard on both the management and the dynamic AP management interface. Please tell me this isn’t the case or that there’s an alternative solution?
Thanks,
Michael
DMZ WLC = 5508 running 7.5.102.0
OEAP = 600
Note: Real IP addresses differ
Solved! Go to Solution.
- Labels:
-
Other Wireless Topics
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-24-2018 08:10 AM - edited 08-24-2018 08:11 AM
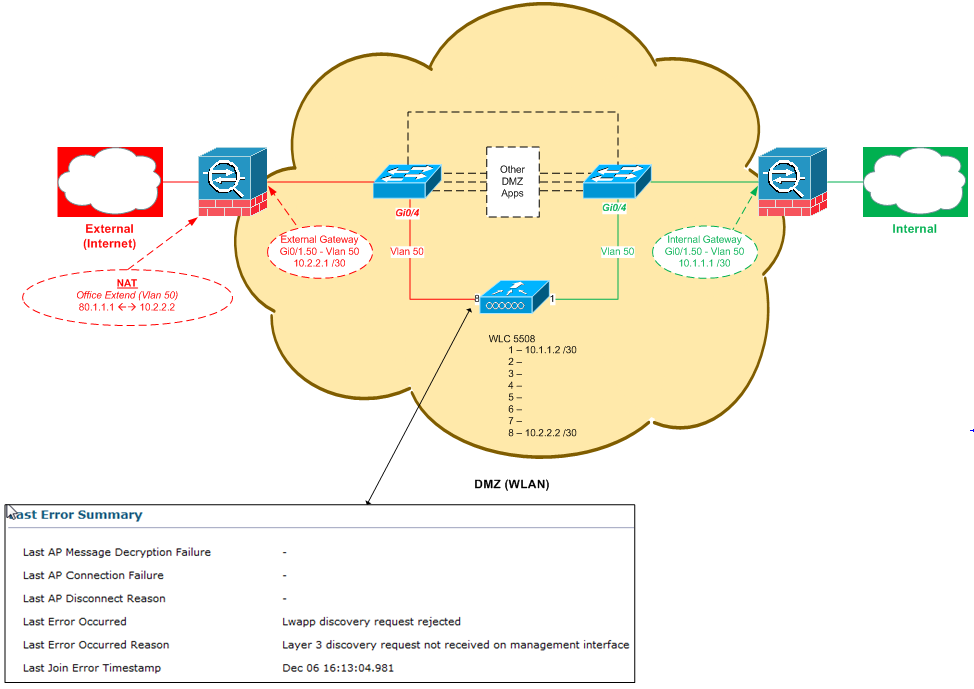
Although it's been a good couple of years since I originally posted my issue I thought it would be a good idea to post the solution in case someone else gets stuck in the same situation. The attached diagram should explain the workaround that was put in place, but basically we added a router in-between the inside and outside to forward the OEAPs response to the WLCs management interface thus allowing the OEAP to join the WLC. Simple yet effective :)
Hope this helps!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2013 04:37 PM
Michael,
The join has to happen on the management interface. All that needs to be done is forward UDP 5246 & UDP 5247 from the outside to the inside management IP address. The management also has the NAT IP address which need to be assigned and is your public address that the OEAP will use to try to join the WLC. You would enable Mac filtering to prevent AP's from joining your WLC. That is how you can filter what AP's or OEAP's can join the WLC. If you had a 2504 or another WLC dedicated for OfficeExtend, you would have that sit on the inside and have the management in the DMZ on port 1 and then you can as sing the other port for access to your inside network. Almost opposite of what your drawing shows.
Sent from Cisco Technical Support iPhone App
*** Please rate helpful posts ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-08-2013 02:27 PM
Thanks for the reply Scott, so just to confirm, you’re saying if I wanted to keep the same physical design the only alternative solution would be to deploy a second WLC dedicated to OE?
But if I keep the same design I would need to make the following changes:
- Increase the subnet for VLAN 50 to a /29
- Readdress Gi0/1.50 on the inside and outside firewall to exist in the same subnet
- Readdress port 1 on the WLC
- Allow VLAN 50 over the inside/outside trunk
- Change outside external firewall rule to NAT to the new port 1/management address
As NATing is already taking place on the firewall, would I really still need to set the management interface to NAT to the public address? Wouldn’t the discovery reply be sent to the external gateway address and then in turn NAT’d to the public address?
Also once the above changes have been made would I be right in thinking that I could remove the outside connection between port 8 (current dynamic management interface) and the outside switch? I can’t see that link being required anymore.
Thanks again,
Michael
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-08-2013 03:21 PM
It's best to keep add a WLC just for OEAP's. Keeping the original design would only work if you open FW ports to the management interface which means that you would not need the port that connects to the DMZ. You have to look at both your OEAP and your local or FlexConnect access points if you change the management to a subnet in the DMZ, you would need to open ports either way and that's not the suggested way.
Sent from Cisco Technical Support iPhone App
*** Please rate helpful posts ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-12-2013 02:43 PM
Ok cool, thanks... As I don't have a spare WLC I went ahead and carried out the changes I mentioned above, and although I can now see the join request being processes (received/sent) by the WLC, the reply is never going to reach the OEAP as its sending the response to ports 1s default gateway which is the inside firewall. Since this interface's used to reach the internal WLC and Prime it's not easily change so I can't really see a suitable work around with this setup... Do you have any more suggestions?
Sent from Cisco Technical Support Android App
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-12-2013 06:27 PM
No other suggestions. AP's have to join using the management interface. Dynamic interface is used to place the traffic.
Sent from Cisco Technical Support iPhone App
*** Please rate helpful posts ***
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-12-2014 09:57 PM
Hi Scott , i have the same problem,
in my deployment i configured the mgmt interface with an internal address, and i created another interface called "dynamic ap managemet" and this ip is mapping with the external address (with NAT)
the configuration guide of wlc 7.6 says that its possible ,
is this correct? or the aps must join using the mgmt interface?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-24-2018 08:10 AM - edited 08-24-2018 08:11 AM
Although it's been a good couple of years since I originally posted my issue I thought it would be a good idea to post the solution in case someone else gets stuck in the same situation. The attached diagram should explain the workaround that was put in place, but basically we added a router in-between the inside and outside to forward the OEAPs response to the WLCs management interface thus allowing the OEAP to join the WLC. Simple yet effective :)
Hope this helps!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide