- Cisco Community
- Technology and Support
- Service Providers
- XR OS and Platforms
- Re: CGN Configuration for BGP Router
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-09-2013 10:42 AM
Hi all,
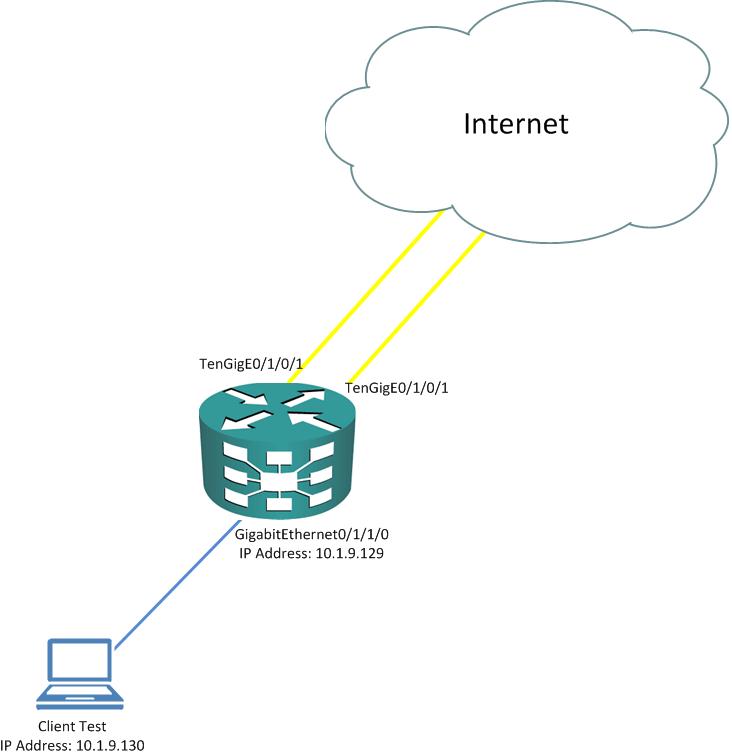
I am in the middle of NAT configuration testing for new ASR9010 implementation. Customer need NAT feature and ordered ISM for the CGN. Need your help to check our configuration and the testing environtment, because we found this configuration didn't work with this testing environtment. The testing environtment is described below.
The configurations are:
-----------------------------------------
!
vrf InsideUserNAT
address-family ipv4 unicast
!
!
vrf InsideWifiNAT
address-family ipv4 unicast
!
!
vrf InsideOfficeNAT
address-family ipv4 unicast
!
!
hw-module service cgn location 0/0/CPU0
!
interface GigabitEthernet0/1/1/0
description NAT Test 1
ipv4 address 10.1.9.129 255.255.255.0
transceiver permit pid all
!
interface GigabitEthernet0/1/1/1
description NAT Test 2
ipv4 address 100.62.16.5 255.255.255.252
transceiver permit pid all
!
interface ServiceApp1
description ASVI for InsideUserNAT
vrf InsideUserNAT
ipv4 address 1.1.1.1 255.255.255.252
service cgn cgn1 service-type nat44
!
interface ServiceApp2
description ASVI for OutsideUserNAT
ipv4 address 2.1.1.1 255.255.255.252
service cgn cgn1 service-type nat44
!
interface ServiceApp3
description ASVI for InsideOfficeNAT
vrf InsideOfficeNAT
ipv4 address 3.1.1.1 255.255.255.252
service cgn cgn1 service-type nat44
!
interface ServiceApp4
description ASVI for OutsideOfficeNAT
ipv4 address 4.1.1.1 255.255.255.252
service cgn cgn1 service-type nat44
!
interface ServiceApp5
description ASVI for InsideWifiNAT
vrf InsideWifiNAT
ipv4 address 5.1.1.1 255.255.255.252
service cgn cgn1 service-type nat44
!
interface ServiceApp6
description ASVI for OutsideWifiNAT
ipv4 address 6.1.1.1 255.255.255.252
service cgn cgn1 service-type nat44
!
interface ServiceInfra1
ipv4 address 100.10.10.1 255.255.255.252
service-location 0/0/CPU0
!
!
router static
address-family ipv4 unicast
100.62.16.0/22 Null0 210
100.62.16.0/24 ServiceApp2
100.62.17.0/24 ServiceApp4
100.62.18.0/24 ServiceApp6
!
vrf InsideUserNAT
address-family ipv4 unicast
0.0.0.0/0 ServiceApp1
10.1.9.0/24 GigabitEthernet0/1/1/0 10.1.9.130
!
!
vrf InsideWifiNAT
address-family ipv4 unicast
0.0.0.0/0 ServiceApp5
!
!
vrf InsideOfficeNAT
address-family ipv4 unicast
0.0.0.0/0 ServiceApp3
!
!
!
service cgn cgn1
service-location preferred-active 0/0/CPU0
service-type nat44 nat1
inside-vrf InsideUserNAT
map ip one-to-one
map address-pool 100.62.16.0/24
!
inside-vrf InsideWifiNAT
map address-pool 100.62.17.0/24
!
inside-vrf InsideOfficeNAT
map address-pool 100.62.18.0/24
!
protocol udp
session active timeout 20
!
!
!
end
RP/0/RSP0/CPU0:BGP-NAT#term leng 24
Wed Jul 10 00:08:35.907 UTC
-----------------------------------------
We can reach internet ip address from GigabitEthernet0/1/1/1. ServiceInfra interface and all serviceapp interfaces are up. Need help check this issue because we will do migration by the end of this week.
Thanks in advance and really appreciate your help.
Solved! Go to Solution.
- Labels:
-
XR OS and Platforms
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-10-2013 12:13 PM
Hi Ingot,
ABF config looks right (one comment, remember that ABF only works for IPv4 traffic, not MPLS, so as long as you receive packets unlabelled, it will work fine).
performance-wise, no particular config is needed and the CGN solution is deployed in many customers without any noticeable impact for final users (the latency induced by the system is absolutely minimal).
Usually, the perf issues are seen when you have MTU issues or load balancing issues (hence my suggestion to try only with one peering interface instead of three).
Since you control the host, I suggest you install wireshark on it and capture traffic, you will probably find what's going on exactly,
Kind regards,
N.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-11-2013 12:42 AM
Hi Nicolas,
Just found the cause of browsing experience problem. There is an issue with ISM module that cause ISM couldn't save the CGN Configuration. I am openning this issue to the TAC. Right now we are waiting for the TAC engineer about this.
Just curious, does CGN support static 1 to 1 NAT maping? Because the customer need the static 1 to 1 mapping, if you have the configuration guide or document related, appreciate if you can share me.
Thanks guys for your help.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-13-2013 10:54 AM
Hi Ingot,
yes 1to1 is available in ISM since 4.2.3 (and you configured it at some point in the configs you shared in this thread).
To quote the feature description:
"The default behavior in the NAT44 translation is many-to-one i.e, multiple private IP addresses can be mapped to a single public IP address. The one-to-one IP translation feature will ensure every public IP address will be mapped to one and only private IP address. However, ports are not restricted. It is enforceable on an inside-vrf basis i.e, it will have to be explicitly configured for each inside-vrf."
Cheers,
N.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-13-2013 08:44 PM
Hi Nicolas,
Sorry, what I mean is Static 1 to 1 NAT. I checked with cisco team already, and they said still on the road map.
But you were right, I configured 1 to 1 maping, thanks for the explanation Nicolas. I really appreciate that.
Cheers,
Ingot.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-22-2013 09:41 PM
Hi All,
We want to ask about ISM scalability issue. The issue are :
1. Each ISM handling 14Gbps of NAT translation.
2. We want to install 6 ISM module to handle 80Gbps NAT traffic from subs.
3. We only have one big bundled interface on the ASR router to the subscriber.
the diagram :
subscriber --- (gateway router) --- (ASR NAT router) --- internet
each link is 80Gig traffic.
(The gateway router) send all 0.0.0.0/0 traffic to (ASR NAT router)
(The gateway router) have bundled-ether(8 TenGElink) interface to (ASR NAT router)
(The gateway router) doesn't have capability to sort/classify/choose which customer ip goes to which interface to internet because of 0.0.0.0/0 to (ASR NAT router)
What is the solution for this, so that (ASR NAT router) can :
1. Can utilize all the ISM prefered active module for all subs.
2. Can have only one big insidevrf assigned to bundle-ether (8 TenGE link). And this one big insidevrf applied to all 6 ISM module.
3. Can use the same insidevrf name for each of all servicecgn that assigned to each of all 6 ISM module.
4. Can use different insidevrf name for each of 6 ISM servicecgn. But the different insidevrf share the same private IP pool from bundle-ether, but different public map pool. (because gateway router only sending 0.0.0.0/0 to ASR NAT and cannot do which subs pool goes to which interface to ASR NAT using route-map/set next hop).
5. Can the ISM module be bundled in one servicecgn. And all NAT process is spreading accross 6 module, and from customer via gateway with default gateway without doing the ACL to specify source of customer pool go to specific interface to get associated with unique vrf that get assigned to specific which ISM doing the nat work. But instead one big bundled of 6 ISM to 1 ISM processing NAT.
Please help.
Thanks,
Budi L
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-22-2013 11:09 PM
Hi Budi,
please use the thread
https://supportforums.cisco.com/message/4022965
for this discussion,
Thanks,
N.
- « Previous
-
- 1
- 2
- Next »
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide