- Cisco Community
- Technology and Support
- Service Providers
- XR OS and Platforms
- Re: ISM with NAT44 - Need help with configuration
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-24-2013 08:07 PM
Hello everyone,
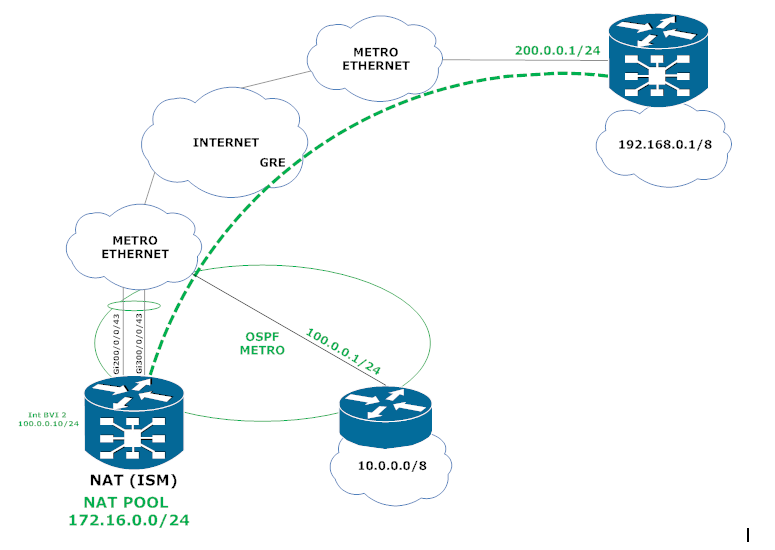
I'm trying to set up NAT44 in the following scenario below and I'm having a hard time figuring out how to redirect the traffic. As you can see the big problem is that I have one single interface that connects to the internal network (10.0.0.0/8) and also to the tunnel destinations all in the same VRF. Can you guys give me a hand? The trafiic comes from network network 10.0.0.0/8 enters interface bundle-ether 2 (Now it needs to be translated), once it is translated, now it needs to reach the destination known via GRE tunnel.
Configurations
-----------------------------------------------
!
vrf NAT_IN
address-family ipv4 unicast
!
!
vrf BLUE
address-family ipv4 unicast
!
!
hw-module service cgn location 0/3/CPU0
!
interface Bundle-Ether2
description UPLINK TO METRO ETHERNET
!
interface Bundle-Ether2.2 l2transport
encapsulation dot1q 2
rewrite ingress tag pop 1 symmetric
!
interface GigabitEthernet200/0/0/43
description LINK TO METRO ETHERNET
bundle id 2 mode active
interface GigabitEthernet300/0/0/43
description LINK TO METRO ETHERNET
bundle id 2 mode active
interface BVI2
description METRO
vrf BLUE
ipv4 address 100.0.0.10/24
!
interface tunnel-ip 101
description GRE_TUNNEL
vrf BLUE
ipv4 address 1.1.1.1/32
tunnel mode gre ipv4
tunnel source interface bvi 2
tunnel destination 200.0.0.1
!
!
interface BVI 100
vrf BLUE
ipv4 address [GATEWAY_100] [MASK_100]
!
interface BVI 200
vrf BLUE
ipv4 address [GATEWAY_200] [MASK_200]
!
interface BVI 300
vrf BLUE
ipv4 address [GATEWAY_300] [MASK_300]
!
!
interface ServiceApp1
vrf NAT_IN
ipv4 address 10.0.2.1 255.255.255.252
service cgn CGN service-type nat44
!
interface ServiceApp2
vrf BLUE
ipv4 address 10.0.2.2 255.255.255.252
service cgn CGN service-type nat44
!
interface ServiceInfra1
ipv4 address 10.0.3.1 255.255.255.0
service-location 0/3/CPU0
!
!
router static
address-family ipv4 unicast
!
vrf NAT_IN
address-family ipv4 unicast
0.0.0.0/0 ServiceApp1
10.0.0.0/8 vrf BLUE bvI 2 <NEXT HOP>
!
!
vrf BLUE
address-family ipv4 unicast
172.16.0.0/24 ServiceApp2
!
!
router ospf METRO
vrf BLUE
router-id [ROUTER_ID]
redistribute bgp 65500 metric 100
area 0
interface bvi 2
!
router ospf BLUE
vrf BLUE
router-id [ROUTER ID]
redistribute bgp 65500 metric 100
area 10
interface BVI100
!
interface BVI200
!
interface BVI200
!
!
!
router bgp 65500
address-family ipv4 unicast
!
address-family vpnv4 unicast
!
!
vrf BLUE
rd 65500:2
address-family ipv4 unicast
redistribute static
redistribute ospf BLUE
!
neighbor 1.1.1.2
remote-as 64512
ebgp-multihop 5
address-family ipv4 unicast
route-policy PASS in
route-policy PASS out
!
!
!
service cgn CGN
service-location preferred-active 0/3/CPU0
service-type nat44 nat44
portlimit 20000
inside-vrf NAT_IN
map outside-vrf BLUE address-pool 172.16.0.0/24
!
!
!
Thanks in advance,
Renato
Solved! Go to Solution.
- Labels:
-
XR OS and Platforms
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2013 07:40 AM
Hi Renato,
The following error msg is coming for the same.
tunl_gre_ea[329]: %PLATFORM-TUNL_GRE_EA_PD-4-UNSUPPORTED_CONFIG : GRE Tunnel not supported on this linecard. Set the network topology to avoid this line card for GRE Tunnel packets
Yes, ISM supports traffic from/to bundle interface (along with physical i/f).
Now, as per your configuration, I see:
- bundle-ether 2 is in NAT_IN VRF and will be receiving inside traffic for NAT. It contains following members:
- GigabitEthernet200/0/0/43
- GigabitEthernet300/0/0/43
- GigabitEthernet200/0/0/43
- bundle-ether 21 is in NAT_OUT and will be receiving outside traffic for NAT. It contains following members:
- TenGigE0/0/0/21
- TenGigE0/0/0/22
- TenGigE0/0/0/21
- ServiceInfra configuration:
interface ServiceInfra1
service-location 0/2/CPU0 -> should be 0/3/cpu0 (if you have ISM is slot 3)
- From NAT perspective, the configuration looks fine.
- bundle-ether 22 is in BLUE containing the following members. As you said, these are connected via loopback
- TenGigE0/1/0/21
- TenGigE0/1/0/22
- TenGigE0/1/0/21
BTW, which version of XR s/w are you using ? Have you installed the Linux install-kit s/w ?
If it is 4.3.x, you can also refer CGv6 Configuration guide, a CCO document, http://www.cisco.com/en/US/docs/routers/asr9000/software/asr9k_r4.3/cg_nat/configuration/guide/cgnat_43.html for installation and configuration steps.
regards,
Somnath.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-01-2013 01:14 AM
Hi Renato,
This is what you have so far (for NAT):
bundle-ether 2 (NAT_IN) -- ISM -- bundle-ether 21 (NAT_OUT).
Now, if you want to send the NAT'ed traffic over a GRE tunnel, you need to do the following:
bundle-ether 2 (NAT_IN) -- ISM -- bundle-ether 21 (NAT_OUT) -- loopback cable(s) -- bundle-ether 22 (BLUE) -- Tunnel-IP 101 (BLUE)
This is because as I mentioned earlier, ISM traffic cannot be sent to / come from GRE tunnel directly.
Let me know if that works.
regards,
Somnath.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-06-2013 02:06 PM
Hi Renato,
One way to solve this restriction would be to have two interfaces (physical or logical) connected to the network. One would be in teh VRF and the other in the global.
Regards
Sr Technical Leader
CCIE 4168 (R&S, SP)
harold@cisco.com
México móvil: +52 1 55 8312 4915
Cisco México
Paseo de la Reforma 222
Piso 19
Cuauhtémoc, Juárez
Ciudad de México, 06600
México
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-04-2013 04:38 AM
Hi Renato,
That's good to hear ! So, you're all set then, I would assume.
regards,
Somnath.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-27-2013 04:59 AM
Hi Renato,
As I understood from your dscription, traffic for NAT enters the box via bundle-ether 2 interface and after NAT should go out via GRE tunnel (interface tunnel-ip 101).
First of all, there are 2 limitations that you should be aware of:
- we don't support (on ISM) NAT traffic to come or go via GRE tunnel i/f (to / from ISM). Hence, one work-around could be to send it via any physical interface and use an external loopback cable and then ultimately send it via GRE tunnel i/f.
- we don't support (on ISM) NAT traffic to come or go via BVI i/f (to / from ISM) as well (not sure, if you're planning to use it for NAT traffic or not).
Once the above 2 are sorted out, NAT configuration would be simple (which you have it almost right). Only thing, you need to have some interface in NAT_IN VRF through which inside NAT traffic enters ASR9K and some interface in BLUE VRF through which outside NAT traffic enters ASR9K.
Let me know if you have more questions.
regards,
Somnath.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-27-2013 08:16 AM
: tunl_gre_ea[329]: %PLATFORM-TUNL_GRE_EA_PD-4-UNSUPPORTED_CONFIG : GRE Tunnel not supported on this linecard. Set the network topology to avoid this line card for GRE Tunnel packets
Can I use a L3 bundle-ether interface in place of a BVI, just in case I need to bundle some interfaces. Does ISM support it or I do have to use a physical interface?
I did another config using using loopback cable (Bundle-Ether21 e Bundle-Ether22), could you check this out?
vrf BLUE
address-family ipv4 unicast
!
vrf NAT_OUT
address-family ipv4 unicast
!
vrf NAT_IN
address-family ipv4 unicast
!
hw-module service cgn location 0/3/CPU0
!
interface Bundle-Ether2
vrf NAT_IN
description UPLINK TO METRO ETHERNET
ipv4 address 100.0.0.10/24
!
interface GigabitEthernet200/0/0/43
description LINK TO METRO ETHERNET
bundle id 2 mode active
!
interface GigabitEthernet300/0/0/43
description LINK TO METRO ETHERNET
bundle id 2 mode active
!
interface Bundle-Ether21
vrf NAT_OUT
ipv4 address 10.0.1.1 255.255.255.0
!
interface Bundle-Ether22
vrf BLUE
ipv4 address 10.0.1.2 255.255.255.0
!
interface TenGigE0/0/0/21
bundle id 21 mode on
!
interface TenGigE0/0/0/22
bundle id 21 mode on
!
interface TenGigE0/1/0/21
bundle id 22 mode on
!
interface TenGigE0/1/0/22
bundle id 22 mode on
!
!
interface tunnel-ip 101
description GRE_TUNNEL
vrf BLUE
ipv4 address 1.1.1.1/32
tunnel mode gre ipv4
tunnel source interface bundle-ether 2
tunnel destination 200.0.0.1
!
!
interface BVI 100
vrf BLUE
ipv4 address [GATEWAY_100] [MASK_100]
!
interface BVI 200
vrf BLUE
ipv4 address [GATEWAY_200] [MASK_200]
!
interface BVI 300
vrf BLUE
ipv4 address [GATEWAY_300] [MASK_300]
!
!
interface ServiceApp1
vrf NAT_IN
ipv4 address 10.0.2.1 255.255.255.0
service cgn CGN service-type nat44
!
interface ServiceApp2
vrf NAT_OUT
ipv4 address 10.0.2.2 255.255.255.0
service cgn CGN service-type nat44
!
interface ServiceInfra1
ipv4 address 10.0.3.1 255.255.255.0
service-location 0/2/CPU0
!
router static
address-family ipv4 unicast
!
vrf NAT_IN
address-family ipv4 unicast
0.0.0.0/0 ServiceApp1
!
!
vrf NAT_OUT
address-family ipv4 unicast
0.0.0.0/0 10.0.1.2
172.16.0.0/24 ServiceApp2
!
!
vrf BLUE
address-family ipv4 unicast
172.16.0.0/24 10.0.1.1
!
!
router ospf METRO
vrf NAT_IN
router-id [ROUTER_ID]
redistribute bgp 65500 metric 100
area 0
interface bundle-ether 2
!
router ospf BLUE
vrf BLUE
router-id [ROUTER ID]
redistribute bgp 65500 metric 100
area 10
interface BVI100
!
interface BVI200
!
interface BVI200
!
!
!
router bgp 65500
address-family ipv4 unicast
!
address-family vpnv4 unicast
!
!
vrf BLUE
rd 65500:2
address-family ipv4 unicast
redistribute static
redistribute ospf BLUE
!
neighbor 1.1.1.2
remote-as 64512
ebgp-multihop 5
address-family ipv4 unicast
route-policy PASS in
route-policy PASS out
!
vrf NAT_IN
rd 65500:3
address-family ipv4 unicast
!
service cgn CGN
service-location preferred-active 0/3/CPU0
service-type nat44 nat44
portlimit 20000
inside-vrf NAT_IN
map outside-vrf NAT_OUT address-pool 172.16.0.0/24
Thanks !
Renato
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2013 07:40 AM
Hi Renato,
The following error msg is coming for the same.
tunl_gre_ea[329]: %PLATFORM-TUNL_GRE_EA_PD-4-UNSUPPORTED_CONFIG : GRE Tunnel not supported on this linecard. Set the network topology to avoid this line card for GRE Tunnel packets
Yes, ISM supports traffic from/to bundle interface (along with physical i/f).
Now, as per your configuration, I see:
- bundle-ether 2 is in NAT_IN VRF and will be receiving inside traffic for NAT. It contains following members:
- GigabitEthernet200/0/0/43
- GigabitEthernet300/0/0/43
- GigabitEthernet200/0/0/43
- bundle-ether 21 is in NAT_OUT and will be receiving outside traffic for NAT. It contains following members:
- TenGigE0/0/0/21
- TenGigE0/0/0/22
- TenGigE0/0/0/21
- ServiceInfra configuration:
interface ServiceInfra1
service-location 0/2/CPU0 -> should be 0/3/cpu0 (if you have ISM is slot 3)
- From NAT perspective, the configuration looks fine.
- bundle-ether 22 is in BLUE containing the following members. As you said, these are connected via loopback
- TenGigE0/1/0/21
- TenGigE0/1/0/22
- TenGigE0/1/0/21
BTW, which version of XR s/w are you using ? Have you installed the Linux install-kit s/w ?
If it is 4.3.x, you can also refer CGv6 Configuration guide, a CCO document, http://www.cisco.com/en/US/docs/routers/asr9000/software/asr9k_r4.3/cg_nat/configuration/guide/cgnat_43.html for installation and configuration steps.
regards,
Somnath.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2013 07:47 AM
Hi Somnath,
Thank you ! I'm using version 4.3.1. I didn`t know I have to install it (haha), is it mandatory?
Thank you again !
Renato
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2013 08:37 AM
Hi Renato,
Yes, installing the Linux install-kit is mandatory as the crux of CGv6 application is part of it.
Please follow the instruction for installing Linux install-kit for 4.2in the CCO document I sent (specifically - http://www.cisco.com/en/US/docs/routers/asr9000/software/asr9k_r4.3/cg_nat/configuration/guide/cgnat43cgn.html#wp1015556). Method for 4.2.1 and above releases is the same.
regards,
Somnath.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2013 08:52 AM
Hi Somnath,
Is it necessary even when I'm using only NAT44? Do you know where I can find the information about the limitations of ISM you mentioned?
Thank you !
Renato
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-28-2013 08:30 PM
Hi Reneto,
Yes, CGv6/CGN functionality is provided by same install-kit. So, you must install the same.
At present, CCO documents are the only external documentation. But, I do see that it does not list some of these limitations. We need to add it to the document.
regards,
Somnath.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2013 10:01 AM
Hi Somnath,
Thank you so much for your attention. I've installed the linux kit and now the module is in
APP-READY state.
Thank you very much again !
Renato
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2013 10:20 AM
You are welcome :-)
That's great ! Now, you can try with some NAT traffic.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2013 10:25 AM
Yeah, I'm going to test it as soon as possible. I'm also having some issue setting up a GRE tunnel on ASR9K, can you help with that or should I open another discussion?
Thanks
Renato Reis
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2013 10:30 AM
Hi Renato,
For GRE tunnel, it would be better to open a separate discussion. You can also check available CCO documentation first to see if you can get answer there. (Reference: http://www.cisco.com/en/US/products/ps9853/products_installation_and_configuration_guides_list.html).
regards,
Somnath.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2013 11:32 AM
Hi Renato,
Could you pelase let us know what kind of issue you have in setting up the GRE tunnel?
Regards
Sr Technical Leader
CCIE 4168 (R&S, SP)
harold@cisco.com
México móvil: +52 1 55 8312 4915
Cisco México
Paseo de la Reforma 222
Piso 19
Cuauhtémoc, Juárez
Ciudad de México, 06600
México
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2013 12:36 PM
Hi Harold,
I've configured a GRE tunnel between 2 ASR9K6 and I'm having the following issues:
1) The tunnel interface is UP but I can't ping the tunnels IP addresses, not even my own tunnel's interface IP address so that I never know if the tunnel is working properly.
2) I don't see the (tunnel vrf [VRF]) on IOS-XR, to tell that my tunnel interface is in VRF BLUE, but my tunnel destination is in VRF NAT_IN.
Configurations
----------------------------------------
ASR01
------------
interface tunnel-ip101
description TUNNEL_1
vrf BLUE
ipv4 address 1.1.1.2 255.255.255.252
tunnel mode gre ipv4
tunnel source Bundle-Ether2
keepalive 10 3
tunnel destination [TUNNEL IP DESTINATION]
!
ASR02
------------
interface tunnel-ip101
description TUNNEL_1
vrf BLUE
ipv4 address 1.1.1.1 255.255.255.252
tunnel mode gre ipv4
tunnel source BVI2
keepalive 10 3
tunnel destination [TUNNEL IP DESTINATION]
Thank you !
Renato
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-29-2013 01:14 PM
Hi Renato,
The VRF aware GRE tunnel currently only supports src/dst resolution in the global routing table. Support for src/dst resolution in a VRF is planned for 5.2.0.
Regards
Sr Technical Leader
CCIE 4168 (R&S, SP)
harold@cisco.com
México móvil: +52 1 55 8312 4915
Cisco México
Paseo de la Reforma 222
Piso 19
Cuauhtémoc, Juárez
Ciudad de México, 06600
México
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

