- Cisco Community
- Technology and Support
- Service Providers
- XR OS and Platforms
- Re: ISM with NAT44 - Need help with configuration
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-24-2013 08:07 PM
Hello everyone,
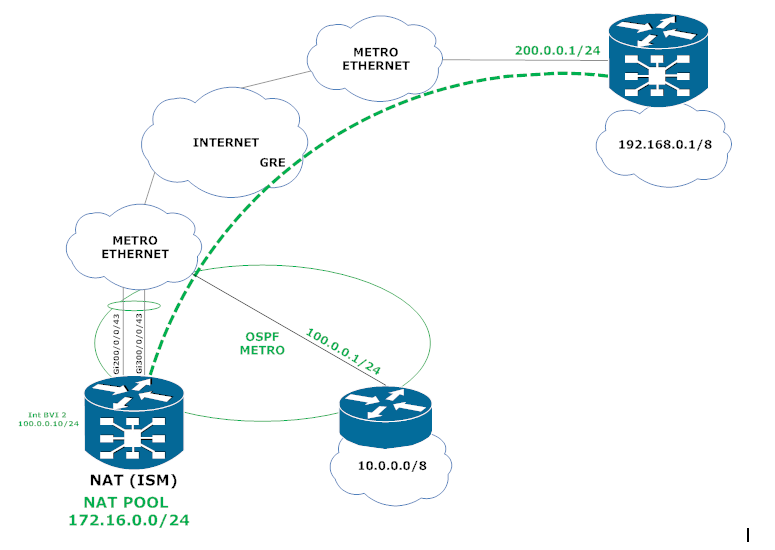
I'm trying to set up NAT44 in the following scenario below and I'm having a hard time figuring out how to redirect the traffic. As you can see the big problem is that I have one single interface that connects to the internal network (10.0.0.0/8) and also to the tunnel destinations all in the same VRF. Can you guys give me a hand? The trafiic comes from network network 10.0.0.0/8 enters interface bundle-ether 2 (Now it needs to be translated), once it is translated, now it needs to reach the destination known via GRE tunnel.
Configurations
-----------------------------------------------
!
vrf NAT_IN
address-family ipv4 unicast
!
!
vrf BLUE
address-family ipv4 unicast
!
!
hw-module service cgn location 0/3/CPU0
!
interface Bundle-Ether2
description UPLINK TO METRO ETHERNET
!
interface Bundle-Ether2.2 l2transport
encapsulation dot1q 2
rewrite ingress tag pop 1 symmetric
!
interface GigabitEthernet200/0/0/43
description LINK TO METRO ETHERNET
bundle id 2 mode active
interface GigabitEthernet300/0/0/43
description LINK TO METRO ETHERNET
bundle id 2 mode active
interface BVI2
description METRO
vrf BLUE
ipv4 address 100.0.0.10/24
!
interface tunnel-ip 101
description GRE_TUNNEL
vrf BLUE
ipv4 address 1.1.1.1/32
tunnel mode gre ipv4
tunnel source interface bvi 2
tunnel destination 200.0.0.1
!
!
interface BVI 100
vrf BLUE
ipv4 address [GATEWAY_100] [MASK_100]
!
interface BVI 200
vrf BLUE
ipv4 address [GATEWAY_200] [MASK_200]
!
interface BVI 300
vrf BLUE
ipv4 address [GATEWAY_300] [MASK_300]
!
!
interface ServiceApp1
vrf NAT_IN
ipv4 address 10.0.2.1 255.255.255.252
service cgn CGN service-type nat44
!
interface ServiceApp2
vrf BLUE
ipv4 address 10.0.2.2 255.255.255.252
service cgn CGN service-type nat44
!
interface ServiceInfra1
ipv4 address 10.0.3.1 255.255.255.0
service-location 0/3/CPU0
!
!
router static
address-family ipv4 unicast
!
vrf NAT_IN
address-family ipv4 unicast
0.0.0.0/0 ServiceApp1
10.0.0.0/8 vrf BLUE bvI 2 <NEXT HOP>
!
!
vrf BLUE
address-family ipv4 unicast
172.16.0.0/24 ServiceApp2
!
!
router ospf METRO
vrf BLUE
router-id [ROUTER_ID]
redistribute bgp 65500 metric 100
area 0
interface bvi 2
!
router ospf BLUE
vrf BLUE
router-id [ROUTER ID]
redistribute bgp 65500 metric 100
area 10
interface BVI100
!
interface BVI200
!
interface BVI200
!
!
!
router bgp 65500
address-family ipv4 unicast
!
address-family vpnv4 unicast
!
!
vrf BLUE
rd 65500:2
address-family ipv4 unicast
redistribute static
redistribute ospf BLUE
!
neighbor 1.1.1.2
remote-as 64512
ebgp-multihop 5
address-family ipv4 unicast
route-policy PASS in
route-policy PASS out
!
!
!
service cgn CGN
service-location preferred-active 0/3/CPU0
service-type nat44 nat44
portlimit 20000
inside-vrf NAT_IN
map outside-vrf BLUE address-pool 172.16.0.0/24
!
!
!
Thanks in advance,
Renato
Solved! Go to Solution.
- Labels:
-
XR OS and Platforms
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-03-2013 10:50 PM
Hi Renato,
SAM modules can be physically removed from the ISM card.
As it is in IN-RESET state, the "show platform summary location 0/3/CPU0" is not able to get App-side version number.
But, as I see the following msg:
"LC/0/3/CPU0:Nov 1 17:24:54.959 : apiv_srvr[115]: %PLATFORM-APIV-5-API_INCOMPATIBLE : Message 24 in APIV module APIV_SI is incompatible (reason: Not supported on the remote side) "
I'm suspecting that the install-kit is not updated properly.
You may need to follow the instructions under http://www.cisco.com/en/US/docs/routers/asr9000/software/asr9k_r4.3/cg_nat/configuration/guide/cgnat43cgn.html#wp1015556.
(I'm assuming Services pie is already installed and only Linux install-kit needs to be installed)
Step 1:
RP/0/RSP0/CPU0(admin)# hw-module location
Step 2:
RP/0/RSP0/CPU0(admin)#debug sim reload-disable location
Step 3:
(Assuming install-kit is already copied to RP)
RP/0/RSP0/CPU0(admin)# download install-image
regards,
Somnath.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-04-2013 01:43 AM
Hi Somnath,
Thank you for your attention. Actually, the FPDs of the new ISM were out of date so that the ISM coudn`t boot up. What I did was shutdown the fib manager process on the card and it no longer reloaded the ISM due to the version incompatibility and then I could upgrade the FPDs and reload the module.
proc mandatory OFF fib_mgr location 0/3/CPU0
proc SHUTDOWN fib_mgr location 0/3/CPU0
RP/0/RSP0/CPU0:router#admin show platform
Mon Nov 4 07:41:48.669 UTC
Node Type State Config State
-----------------------------------------------------------------------------
0/RSP0/CPU0 A9K-RSP440-TR(Active) IOS XR RUN PWR,NSHUT,MON
0/RSP1/CPU0 A9K-RSP440-TR(Standby) IOS XR RUN PWR,NSHUT,MON
0/FT0/SP FAN TRAY READY
0/FT1/SP FAN TRAY READY
0/0/CPU0 A9K-MOD160-TR IOS XR RUN PWR,NSHUT,MON
0/0/0 A9K-MPA-8X10GE OK PWR,NSHUT,MON
0/0/1 A9K-MPA-8X10GE OK PWR,NSHUT,MON
0/1/CPU0 A9K-MOD160-TR IOS XR RUN PWR,NSHUT,MON
0/1/0 A9K-MPA-8X10GE OK PWR,NSHUT,MON
0/1/1 A9K-MPA-8X10GE OK PWR,NSHUT,MON
0/3/CPU0 A9K-ISM-100(LCP) IOS XR RUN PWR,NSHUT,MON
0/3/CPU1 A9K-ISM-100(SE) APP-READY
0/PM0/SP PWR-3KW-AC-V2 READY PWR,NSHUT,MON
0/PM1/SP PWR-3KW-AC-V2 READY PWR,NSHUT,MON
0/PM2/SP PWR-3KW-AC-V2 READY PWR,NSHUT,MON
RP/0/RSP0/CPU0:router#
Thank you so much,
Renato
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-04-2013 04:38 AM
Hi Renato,
That's good to hear ! So, you're all set then, I would assume.
regards,
Somnath.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-04-2013 08:57 AM
Hi Somnath,
I just wanna ask if you have any extra material about the SAM modules? How can I use them?
Thanks,
Renato Reis
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-04-2013 07:23 PM
Hi Renato,
SAM module is already EOLed (http://www.cisco.com/en/US/prod/collateral/routers/ps9853/end_of_life_notice_c51-721386.html).
You do not need those for running CGv6 application - those are not used by CGv6 application software.
Details about how to handle / OIR SAM module are available at http://www.cisco.com/en/US/docs/routers/asr9000/hardware/ism_line_card/installation/guide/ismiginstalling.html#wp865031.
regards,
Somnath.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-18-2013 03:17 AM
Hi Somnath,
Let's see if you can help with this new scenario. I want to extend this NAT configuration to a new site (BO1), but instead of using this entire setup with ASR9K, etc, I just want to use ASR9000v module and have this AS9K + ISM as the host. The first problem I see in this scenario is that I have the same 10.0.0.0/8 network in both sites, network which will access the same resources as the devices in the 10.0.0.0/8 in the main site.
1) Do you think if I create a new inside VRF [NAT_IN1] would address this issue?
2) Can I use the same outside VRF?

Here is the configurations.
!! IOS XR Configuration 4.3.1
!
vrf NAT_IN
address-family ipv4 unicast
import route-target
65500:2
65500:3
!
export route-target
65500:3
!
!
!
vrf RED
address-family ipv4 unicast
import route-target
65500:1
!
export route-target
65500:1
!
!
!
vrf NAT_OUT
address-family ipv4 unicast
import route-target
65500:4
!
export route-target
65500:4
!
!
!
vrf SATELLITE
!
vrf BLUE
address-family ipv4 unicast
import route-target
65500:2
!
export route-target
65500:2
!
!
!
hw-module service cgn location 0/3/CPU0
!
ipv4 access-list ABF
5 permit ospf any any
10 permit ipv4 any 10.200.0.0 0.0.255.255 nexthop1 vrf NAT_IN ipv4 10.0.2.2
20 permit icmp any any
!
interface Bundle-Ether3
description Uplink (BE3 - VRF NAT_IN) - VLAN 20
vrf NAT_IN
ipv4 address 1.1.1.1 255.255.255.0
ipv4 access-group ABF ingress
!
!
interface Bundle-Ether22
description LOOPBACK CABLE NAT_OUT
vrf NAT_OUT
ipv4 address 10.0.1.1 255.255.255.0
!
!
interface Bundle-Ether23
description LOOPBACK CABLE BLUE
vrf BLUE
ipv4 address 10.0.1.2 255.255.255.0
!
!
interface 6
description Uplink (BE6 - Global) - VLAN 20,51,80-82
!
!
interface 6.2
ipv4 address 1.1.1.2 255.255.255.0
encapsulation dot1q 2
!
interface 6.51 l2transport
description EFP - BE6 - VLAN 51
encapsulation dot1q 51
rewrite ingress tag pop 1 symmetric
!
interface 6.80 l2transport
description EFP - BE6 - VLAN 80
encapsulation dot1q 80
rewrite ingress tag pop 1 symmetric
!
interface 6.81 l2transport
description EFP - BE6 - VLAN 81
encapsulation dot1q 81
rewrite ingress tag pop 1 symmetric
!
interface 6.82 l2transport
description EFP - BE6 - VLAN 82
encapsulation dot1q 82
rewrite ingress tag pop 1 symmetric
!
interface Bundle-Ether100
description Bundle to Satellite 100
vrf SATELLITE
ipv4 point-to-point
ipv4 unnumbered Loopback0
nv
satellite-fabric-link satellite 100
remote-ports GigabitEthernet 0/0/0-43
!
!
!
interface Bundle-Ether200
description Bundle to Satellite 200
vrf SATELLITE
ipv4 point-to-point
ipv4 unnumbered Loopback0
nv
satellite-fabric-link satellite 200
remote-ports GigabitEthernet 0/0/0-43
!
!
!
interface Bundle-Ether300
description Bundle to Satellite 300
vrf SATELLITE
ipv4 point-to-point
ipv4 unnumbered Loopback0
nv
satellite-fabric-link satellite 300
remote-ports GigabitEthernet 0/0/0-35
!
!
!
interface Loopback0
description MGMT SATELLITE
vrf SATELLITE
ipv4 address 10.0.0.254 255.255.255.0
!
interface tunnel-ip31101
description BLUE-TUNNEL01
vrf BLUE
ipv4 address 10.200.253.90 255.255.255.252
tunnel mode gre ipv4
tunnel source 6.2
tunnel destination 13.13.13.13
!
interface tunnel-ip31102
description BLUE-TUNNEL02
vrf BLUE
ipv4 address 10.200.253.94 255.255.255.252
tunnel mode gre ipv4
tunnel source 6.2
tunnel destination 14.14.14.14
!
interface tunnel-ip31103
description RED-TUNNEL03
vrf RED
ipv4 address 10.200.253.90 255.255.255.252
tunnel mode gre ipv4
tunnel source 6.2
tunnel destination 13.13.13.13
!
interface tunnel-ip31104
description RED-TUNNEL04
vrf RED
ipv4 address 10.200.253.94 255.255.255.252
tunnel mode gre ipv4
tunnel source 6.2
tunnel destination 14.14.14.14
!
!
interface TenGigE0/0/0/0
description LINK TO SATELLITE 100
bundle id 100 mode on
!
interface TenGigE0/0/0/1
description LINK TO SATELLITE 100
bundle id 100 mode on
!
interface TenGigE0/0/0/2
description LINK TO SATELLITE 200
bundle id 200 mode on
!
interface TenGigE0/0/0/3
description LINK TO SATELLITE 200
bundle id 200 mode on
!
interface TenGigE0/0/0/4
description LINK TO SATELLITE 300
vrf SATELLITE
ipv4 point-to-point
ipv4 unnumbered Loopback0
nv
satellite-fabric-link satellite 300
remote-ports GigabitEthernet 0/0/36-43
!
!
!
interface TenGigE0/0/0/5
description LINK TO SATELLITE 300
bundle id 300 mode on
!
!
interface TenGigE0/0/0/16
description UPLINK (BE6 - GLOBAL) - VLAN 20,51,80-82
bundle id 6 mode active
!
interface TenGigE0/1/0/16
description UPLINK (BE6 - GLOBAL) - VLAN 20,51,80-82
bundle id 6 mode active
!
!
interface TenGigE0/0/0/17
description UPLINK (BE3 - VRF NAT_IN) - VLAN 20
bundle id 3 mode active
!
!
interface TenGigE0/1/0/17
description UPLINK (BE3 - VRF NAT_IN) - VLAN 20
bundle id 3 mode active
!
!
interface TenGigE0/0/0/22
description LOOPBACK CABLE TE0/1/0/22
bundle id 22 mode on
!
interface TenGigE0/0/0/23
description LOOPBACK CABLE TE0/1/0/23
bundle id 22 mode on
!
interface TenGigE0/1/0/0
description LINK TO SATELLITE 100
bundle id 100 mode on
!
interface TenGigE0/1/0/1
description LINK TO SATELLITE 100
bundle id 100 mode on
!
interface TenGigE0/1/0/2
description LINK TO SATELLITE 200
bundle id 200 mode on
!
interface TenGigE0/1/0/3
description LINK TO SATELLITE 200
bundle id 200 mode on
!
interface TenGigE0/1/0/4
description LINK TO SATELLITE 300
bundle id 300 mode on
!
interface TenGigE0/1/0/5
description LINK TO SATELLITE 300
bundle id 300 mode on
!
!
!
interface TenGigE0/1/0/22
description LOOPBACK CABLE TE0/0/0/22
bundle id 23 mode on
!
interface TenGigE0/1/0/23
description LOOPBACK CABLE TE0/0/0/23
bundle id 23 mode on
!
interface BVI30
vrf RED
ipv4 address 10.200.25.193 255.255.255.192
!
interface BVI31
vrf BLUE
ipv4 address 10.200.1.1 255.255.255.248
!
interface BVI32
vrf BLUE
ipv4 address 10.200.25.129 255.255.255.224
!
interface BVI33
vrf BLUE
ipv4 address 10.200.25.1 255.255.255.128
!
interface BVI36
vrf BLUE
ipv4 address 10.200.237.145 255.255.255.240
!
interface BVI51
vrf RED
ipv4 address 192.168.7.12 255.255.255.0
!
interface BVI80
vrf RED
ipv4 address 10.200.26.169 255.255.255.224
!
interface BVI81
vrf BLUE
ipv4 address 10.200.25.164 255.255.255.240
!
interface BVI82
vrf BLUE
ipv4 address 10.200.25.180 255.255.255.240
!
!
interface ServiceApp1
description NAT_IN
vrf NAT_IN
ipv4 address 10.0.2.1 255.255.255.252
service cgn CGN service-type nat44
!
interface ServiceApp2
description NAT_OUT
vrf NAT_OUT
ipv4 address 10.0.2.5 255.255.255.252
service cgn CGN service-type nat44
!
interface ServiceInfra1
description ISM
ipv4 address 10.0.3.1 255.255.255.0
service-location 0/3/CPU0
!
!
prefix-set PS_ROUTES
10.200.0.8,
10.200.5.40/29,
10.200.1.0/29,
10.200.5.32/29,
10.200.0.144/28,
10.200.106.0/28,
10.200.106.16/28
end-set
!
prefix-set PS_BGP_BLUE_OUT
10.200.24.192/26,
10.200.5.40/29,
10.200.240.0/25,
10.200.1.0/29,
10.200.25.128/27,
10.200.25.0/25,
10.200.5.32/29,
10.200.26.0/25,
10.200.0.144/28,
10.200.27.128/27,
10.200.27.0/25,
10.200.106.0/28,
10.200.106.128/25,
10.200.106.16/28,
10.200.107.128/25
end-set
!
route-policy RP_DENY_ALL
drop
end-policy
!
route-policy RP_PASS_ALL
pass
end-policy
!
route-policy RP_BGP_BLUE_OUT
if destination in PS_BGP_BLUE_OUT then
pass
endif
end-policy
!
route-policy RP_PASS_ROUTES
if destination in PS_ROUTES then
pass
endif
end-policy
!
!
router static
address-family ipv4 unicast
0.0.0.0/0 1.1.1.20
!
vrf NAT_IN
address-family ipv4 unicast
0.0.0.0/0 ServiceApp1
!
!
vrf RED
!
vrf NAT_OUT
address-family ipv4 unicast
0.0.0.0/0 10.0.1.2
10.200.24.192/26 ServiceApp2
!
!
vrf BLUE
address-family ipv4 unicast
10.200.24.192/26 10.0.1.1
!
!
!
router ospf
log adjacency changes
vrf NAT_IN
router-id 1.1.1.1
disable-dn-bit-check
redistribute bgp 65500 metric 5 metric-type 2 route-policy RP_PASS_ROUTES
!
area 7
interface Bundle-Ether3
!
!
!
!
router ospf RED
log adjacency changes
vrf RED
router-id 10.200.26.169
disable-dn-bit-check
redistribute bgp 65500 metric 10 metric-type 2
area 11
interface BVI30
!
interface BVI80
!
!
!
!
router ospf BLUE
log adjacency changes
vrf BLUE
router-id 10.200.25.164
disable-dn-bit-check
redistribute static
redistribute bgp 65500 metric 10 metric-type 2
area 0
interface BVI81
!
interface BVI82
!
!
area 2
interface BVI31
!
interface BVI32
!
interface BVI33
!
interface BVI36
!
!
!
!
router bgp 65500
address-family ipv4 unicast
!
address-family vpnv4 unicast
!
vrf NAT_IN
rd 65500:3
bgp router-id 1.1.1.1
address-family ipv4 unicast
route-target download
!
!
vrf RED
rd 65500:1
bgp router-id 10.200.253.90
address-family ipv4 unicast
network 10.200.25.192/26
network 10.200.26.128/27
network 10.200.26.192/27
network 10.200.27.192/26
network 10.200.104.128/27
network 10.200.104.160/27
!
neighbor 10.200.253.89
remote-as 64512
ebgp-multihop 5
update-source tunnel-ip31103
address-family ipv4 unicast
route-policy RP_PASS_ALL in
route-policy RP_PASS_ALL out
soft-reconfiguration inbound
!
!
neighbor 10.200.253.93
remote-as 64512
ebgp-multihop 5
update-source tunnel-ip31104
address-family ipv4 unicast
route-policy RP_PASS_ALL in
route-policy RP_PASS_ALL out
soft-reconfiguration inbound
!
!
!
vrf BLUE
rd 65500:2
bgp router-id 10.200.253.90
address-family ipv4 unicast
network 10.200.0.144/28
network 10.200.1.0/29
network 10.200.5.32/29
network 10.200.5.40/29
network 10.200.24.192/26
network 10.200.25.0/25
network 10.200.25.128/27
network 10.200.26.0/25
network 10.200.27.0/25
network 10.200.27.128/27
network 10.200.106.0/28
network 10.200.106.16/28
network 10.200.106.128/25
network 10.200.107.128/25
network 10.200.240.0/25
!
neighbor 10.200.253.89
remote-as 64512
ebgp-multihop 5
update-source tunnel-ip31101
address-family ipv4 unicast
route-policy RP_PASS_ALL in
route-policy RP_BGP_BLUE_OUT out
soft-reconfiguration inbound
!
!
neighbor 10.200.253.93
remote-as 64512
ebgp-multihop 5
update-source tunnel-ip31102
address-family ipv4 unicast
route-policy RP_PASS_ALL in
route-policy RP_BGP_BLUE_OUT out
soft-reconfiguration inbound
!
!
!
!
l2vpn
load-balancing flow src-dst-ip
bridge group VLAN30
bridge-domain VLAN30
!
!
routed interface BVI30
!
!
bridge group VLAN31
bridge-domain VLAN31
!
!
routed interface BVI31
!
!
bridge group VLAN32
bridge-domain VLAN32
routed interface BVI32
!
!
bridge group VLAN33
bridge-domain VLAN33
!
routed interface BVI33
!
!
bridge group VLAN36
bridge-domain VLAN36
!
routed interface BVI36
!
!
bridge group VLAN51
bridge-domain VLAN51
!
routed interface BVI51
!
!
bridge group VLAN80
bridge-domain VLAN80
interface 6.80
!
routed interface BVI80
!
!
bridge group VLAN81
bridge-domain VLAN81
interface 6.81
!
routed interface BVI81
!
!
bridge group VLAN82
bridge-domain VLAN82
interface 6.82
!
routed interface BVI82
!
!
!
nv
satellite 100
type asr9000v
ipv4 address 10.0.0.1
!
satellite 200
type asr9000v
ipv4 address 10.0.0.2
!
satellite 300
type asr9000v
ipv4 address 10.0.0.3
!
!
!
service cgn CGN
service-location preferred-active 0/3/CPU0
service-type nat44 nat44
portlimit 20000
inside-vrf NAT_IN
map outside-vrf NAT_OUT address-pool 10.200.24.192/26
!
!
!
Thanks in advance,
Renato
- « Previous
- Next »
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide