Introduction:
Firepower 2100 series platform can run either FTD or ASA software.
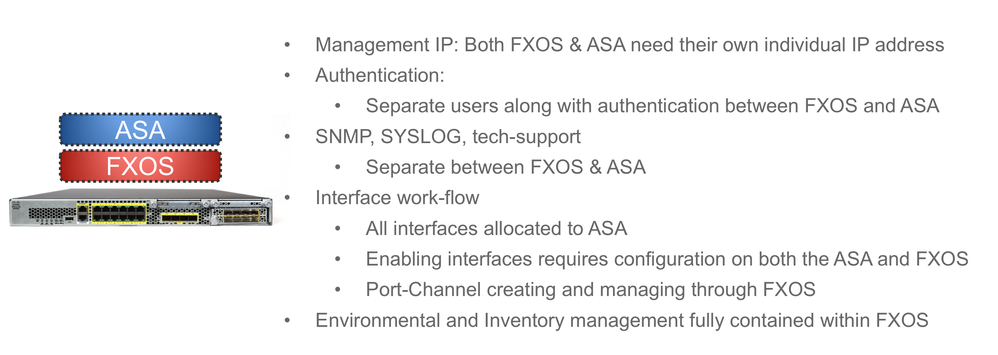
When Firepower 2100 series platform running ASA, has two software, FXOS and ASA. Both have its own management IP address and share same physical Interface Management 1/1.
Both ASA and FXOS has its own authentication, same with SNMP, Syslog and tech-support logs.
Toggle between FXOS & ASA prompt:
From FXOS prompt, you can use "connect asa" to go to ASA prompt, "exit" to come back to FXOS.
From ASA prompt, you can use "connect fxos" to go to FXOS prompt, "exit" to come back to ASA.
When using Console, you'll login to fxos prmpt.
ssh/telnet to ASA Management IP to access ASA.
ssh to fxos management IP to access FXOS.
ASA & FXOS Management:
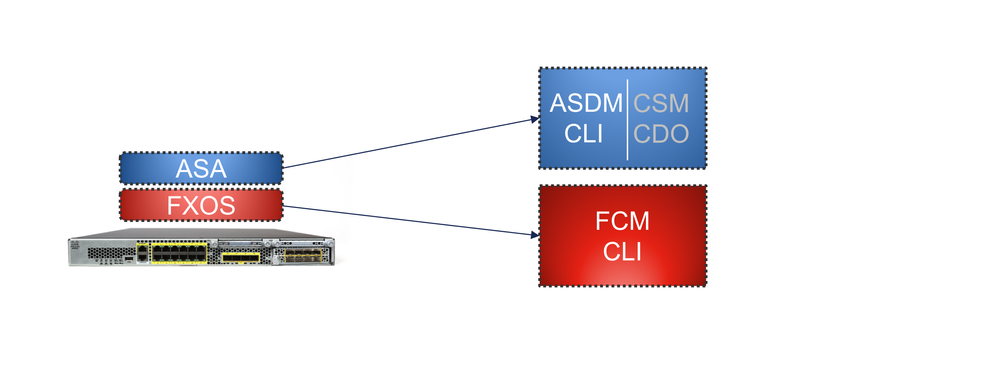
In order to manage ASA, you have ASDM or CLI (SSH, Telnet). To manager FXOS, we have CLI and FCM-Firepower Chassis Manager - Browser base GUI tool.
FXOS useful configurations:-
The Default IP address for FXOS IP address for FP2100 running ASA is 192.168.45.45.
Verify & Configuring Management IP address for FXOS:-
To Verify FXOS IP address
firepower-2110# scope fabric-interconnect a
firepower-2110 /fabric-interconnect # show detail
Fire Power:
ID: A
Product Name: Cisco FPR 2110
PID: FPR-2110
VID: V01
Vendor: Cisco Systems, Inc.
Serial (SN): JMX202820M4
OOB IP Addr: 192.168.45.45
OOB Netmask: 255.255.255.0
OOB Gateway: 192.168.45.1
OOB Gateway Use DataPort: No
OOB Boot Proto: Static
OOB IPv6 Address: ::
Prefix: 64
OOB IPv6 Gateway: ::
OOB IPv6 Gateway Use DataPort: No
IPv6 Boot Proto: Static
DHCPD Admin State: DHCP Server Enabled
Changing FXOS management IP address:
firepower# scope fabric-interconnect a
firepower /fabric-interconnect # set out-of-band static ip 10.106.143.40 netmask 255.255.255.0 gw 10.106.143.1
firepower /fabric-interconnect* # commit-buffer (Commit buffer to save config)
some time you may get below error:
" Error: Update failed: [Management ipv4 address (IP 10.106.143.40 / net mask 255.255.255.0 ) is not in the same network of current DHCP server IP range 192.168.45.5 - 192.168.45.10. Either disable DHCP server first or config with a different ipv4 address.] "
If you get above error, you need to either disable DHCP or change DHCP range in the same subnet as new Management IP address.
Disabling DHCP Server:
firepower# scope system
firepower /system* # scope services
firepower /system* # disable dhcp-server
or
firepower /system* # enable dhcp-server 10.106.143.10 10.106.143.20 (To enable DHCP server on FXOS)
Setting Time/Timezone/NTP:
Configuring NTP or timezone on ASA running on FP2100 is restricted. Clock, timezone,ntp need to be configured on FXOS, which will be sync to ASA.
firepower# scope system
firepower /system* # scope services
firepower /system/services *# set clock oct 6 2017 17 12 00
firepower /system/services *# set timezone
firepower /system/services *# create ntp-server <ntp-server host/ip address>
firepower /system/services *# commit-buffer (Commit buffer to save config)
DNS Configuration:
firepower# scope system
firepower /system* # scope services
firepower /system/services *# create dns 8.8.8.8 0
firepower /system/services *# create dns 203.10.5.1 1
firepower /system/services *# commit-buffer (Commit buffer to save config)
Discard Changes:
"discard-buffer" can be used to discard changes before committing any changes.
