Hi Everyone
at this Article we want to talk about very commonly project in network security section, and today's Network security is bolder than old, and we see some article about Security but they have only some theoretical info, in this Article we want to have a very common security feature in CISCO or any other switches( Management switches ), its about Port Security. How you can manage your Security of your network ? maybe you have a wireless network, in this situation you must select another solution or maybe you have different scenario with different hardware or virtualization and you have another option with different name for implement basic Access security .
In this Article we visualize we have an Ethernet Network with simple equipment and as refer to Ethernet standard each device have a MAC Address.
so how we can secure our network ? we have so many security solution but some of there is:
-DHCP Snooping :
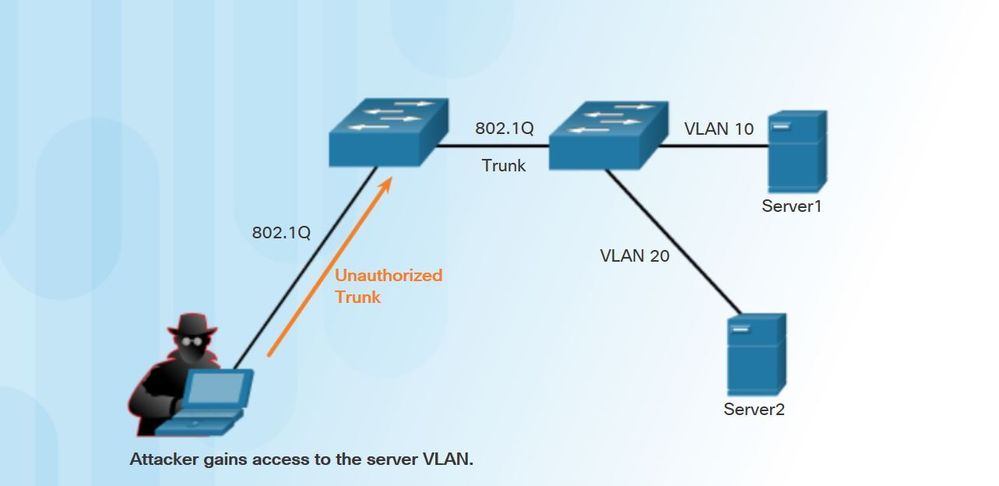
Attacker can run a DHCP Server on here PC or device then get Address to your Network devices, maybe you think its good, cause your DHCP Server use less CPU and Attacker computer help it, but Attacker do that for here destiny, for example set Default Gateway or DNS of here system and then can very easily redirect your network traffic to capture or any other use.
or another attack is send so many IP Address request to DHCP and used capacity of your DHCP pool.
-Dynamic ARP Protection: Protects your network from ARP cache poisoning.
refer to Ethernet standard and how ARP working, as you know, ARP table filled via frames come to your nodes, Ethernet device extract source of that device and if it wasn't in here CAM Table then add it (of course for unicast Address ) so today's i can very easily create or build an script with Ruby, Python , .... that send crafted frame to Network, for example i can create empty frame with source address of my Router MAC and destination MAC address of another node then send it to Network, what happened if you haven't enough security implementation on your central devices like switches ? when destination node receive this frame extract it Source MAC address then Extract source IP Address and see the MAC address of her gateway or router was changed so it change here CAM Table, after that if this node want to send any data to her gateway, create an frame with this information: Destination IP Address: Router Address | Destination MAC Address: Attacker MAC Address
and what can be happened ? all of traffic send to the Attacker device. OK for prevent this type of Attack we can use ARP Protection Method.
Port Security Configuration:
select Interface or interface range
switchport port-security
set maximum MAC Address can be assigned to this port:
switchport port-security maximum XXX
set Violation mode to what happen when maximum number of MAC Address rich :
switchport port-security violation XXXX
Add manually MAC Address to MAC Table that allow forward Frames:
switchport port-security mac-address mac_address
Enable sticky Learning MAC Address of each node connected to this port(unless maximum number rich)
switchport port-security mac-address sticky
show port security status of all ports you enable it:
show port-security
Show Address learned of all Interfaces :
show port-security address
show Address of specify port that allow forward traffic:
show port-security address interface interface_id
