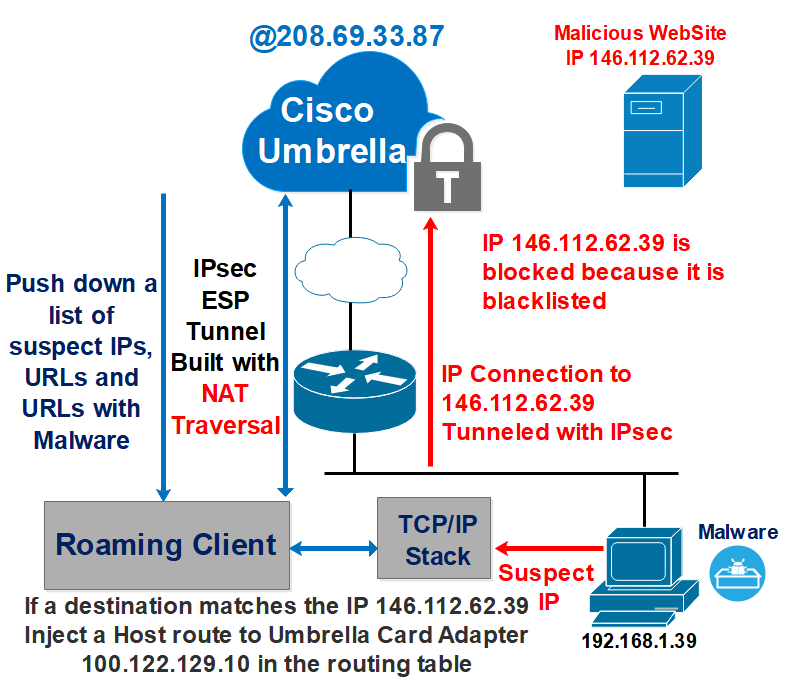
Cisco Umbrella is a big DNS service that provides not only the DNS resolution but also if the hosted website is trust or malicious, the idea behind the Layer DNS Security is that the modern attacks uses the DNS in the first step either to redirect the user to a malicious website or after the infection is happened through the installation of a malware, the first thing the malware will do, is to try to find out the Command and Control server in order to receive instructions by using the DNS to find the IP address, the DNS request is redirected to the Umbrella and the attempts is blocked.
Now the question is what if the infected host does not use the DNS to reach out the Command and Control server? instead it uses the IP address to establish an IP connection with the C&C in order to bypass umbrella.
Here comes a very useful feature called IP Layer Enforcement, this is exactly similar to Security Intelligence feature in Firepower Threat Defense. The goal is to enforce the IP Layer Security in addition of DNS Layer Security.
The most interesting question for an administrator is: How the IP Layer Enforcement Works?
After testing using Wireshark, the process is very interesting:
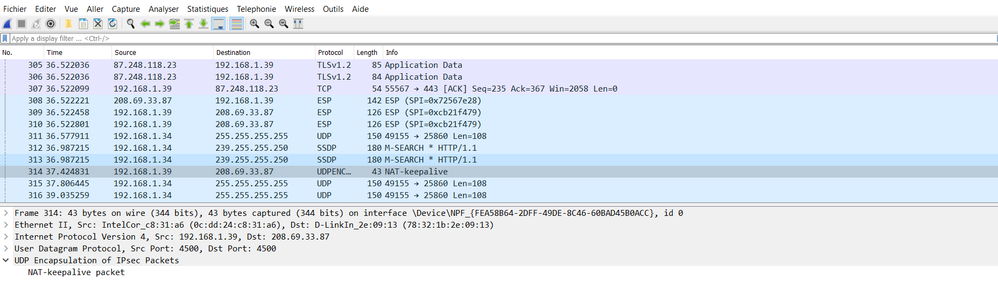
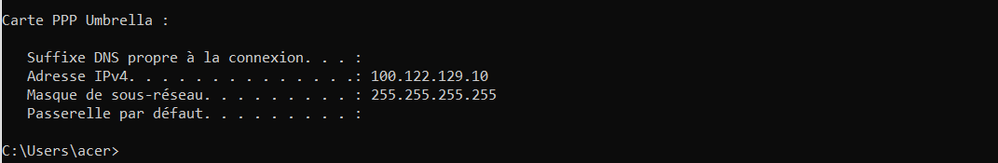
1-The Roaming Client builts an IPsec Tunnel using ESP. The Tunnel source is the user 192.168.1.39 and the Tunnel Destination is 208.69.33.87.
Since the host 192.168.1.39 is behind a NAT device, at the router facing internet, the source of the ESP packet is changed so, the NAT traversal mechanism is needed to establish the tunnel successfully, the roaming client send a NAT-Keeplive packet to detect if a NAT is present along the path.
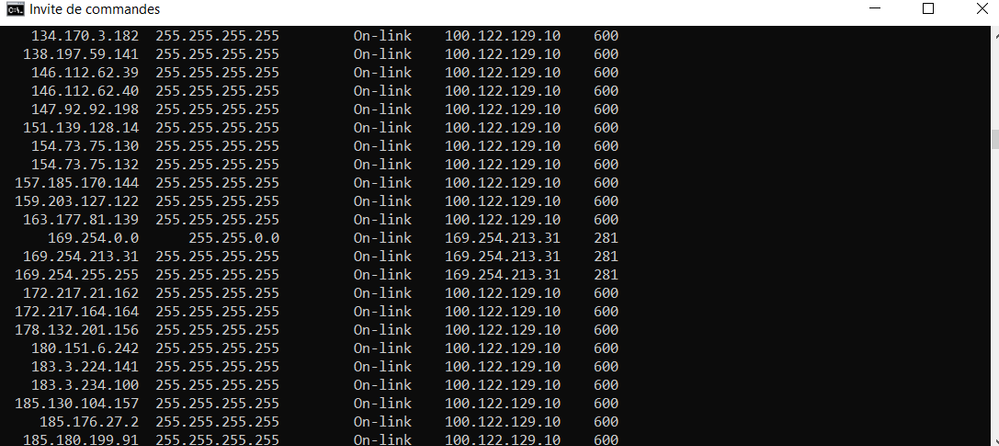
2-The Umbrella Roaming client download the list of suspect IPs.
3-When the infected host initiates an IP connection to 146.112.62.39.
4 The Roaming Client sees that the IP 146.112.62.39 is blacklisted.
It injects a host route in the routing table of the host, the destination is 146.112.62.39 and the outgoing interface is the Umbrella Adapter Card 100.122.129.10.
5-Finally the initial IP connection is sent through the IPsec Tunnel , and received and blocked by umbrella.
Below how it works with simple example: