- Cisco Community
- Technology and Support
- Security
- Security Blogs
- Wireless Hacking
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Understanding Wireless Technology
According to Wikipedia,
Wireless communication is the transfer of information without the use of wires. The distances involved may be short (a few meters as in television remote control) or long (thousands or millions of kilometers for radio communications). The term is often shortened to "wireless".

Wireless Network Setup:
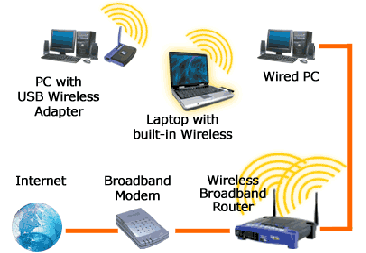
Generally a wireless network consists of three components. :
- 802.11a/b/g/n devices.
- Wireless Access Points.
- Optionally, the network might contain an additional gateway which acts as an interface to the internet
Wireless Standards:
- 802.11 (legacy) : First wireless standard. Created in 1997. It is obsolete now. Speeds of 1,2 Mbps are supported.
- 802.11a: Created in 1999, Supports speeds of 6, 9, 12, 18, 24, 36, 48, 54 Mbps.
- 802.11b: Also created in 1999, Supports speeds of 5.5, 11 Mbps.
- 802.11g: Created in 2003, Supports speeds of 6, 9, 12, 18, 24, 36, 48, 54 Mbps.
- 802.11n: Created in 2009, it can supports speeds upto 150Mbps.
Types of Wireless Network Layouts:
- Peer-to-peer – Also called adhoc wireless LAN, is a network where stations communicate only peer to peer (P2P). There is a lack of a controlling base.
- Access Points – In this scenario, the wireless network represents a client-server model in which special Access Points act as central server onto which multiple wireless clients can connect
- Wireless distribution system – Wireless Distribution System is a system that enables the wireless interconnection of access points. It allows a wireless network to be expanded using multiple access points without the need for a wired backbone to link them, as is traditionally required.
- Extension to a wired network – This concept involves extending a wired network over wireless. An example could be wifi routers attached with ADSL modems.
Detecting Wireless Network:
Detecting a wireless network can be pretty straight forward, if the wireless AP is not set as hidden. The following ways can be used to detect wireless networks.
- Using operating system wireless monitors.
- Using handheld devices (such as wifi enabled cellphones). Also special software can be used on top of those cellphones which further aid this. (eg. WifiEye and Barbelo).
- Using passive scanners (Tool: Kismet, KisMAC).
- Using active beacon scanners (Tool: NetStumbler, MacStumbler, iStumbler).
Wireless Security standards:
The issues with the security of SSID led to the development and usage of wireless protocols and standards. The important standards are:
- Wired Equivalent Privacy (WEP)
- Wi-Fi Protected Access (WPA)
- Wi-Fi Protected Access v2 (WPA2)
Wireless Equivalent Privacy (WEP):
- WEP is a component of the IEEE 802.11 WLAN standards. Its primary purpose is to provide for confidentiality of data on wireless networks at a level equivalent to that of wired LANs.
- WEP accomplished eavesdropping by encrypting data with the RC4 encryption algorithm.
- WEP, however is weak and can be broken with minimum efforts.
Wi-Fi Protected Access (WPAv1):
- WPAv1 comes in two variants, WPA Enterprise and WPA PSK
- WPA Enterprise provides RADIUS based authentication using 802.1x.
- WPA Personal or PSK uses a pre shared key.
Wi-Fi Protected Access (WPAv2):
- WPAv2 also comes in two variants, WPA Enterprise and WPA PSK
- WPA Enterprise provides RADIUS based authentication using 802.1x.
- Difference b/w WPAv1 and WPAv2 is the fact that WPAv2 has to mandatorily include AES-CCMP algorithm. It reinforces the security of WPAv2.
MAC Sniffing & ARP Spoofing:
- Since MAC Address must appear in the clear even when WEP is enabled, they can be easily sniffed.
- An attacker can spoof his MACaddress as any of the available and connected MAC address and bypass MAC based restrictions.
- Using simple packet-capturing software, anyone can identify a valid MAC address using one packet. Spoofing MAC addresses is very easy.
- To perform a spoofing attack, an attacker must set up an access point (rogue) near the target wireless network or in a place where a victim may believe that wireless Internet is available.
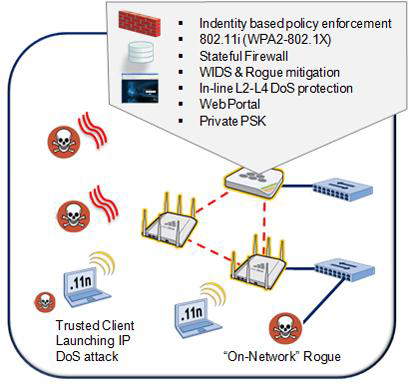
Denial-of-Service attacks:
- Denial of service attacks can be unleashed on WLANs.
- Since WLANs send information in predetermined channels and frequencies, DOS attacks can be done when noise is broadcasted over same channels.
Man-in-the-Middle Attack( MITM):
Two types of MITM:
Eavesdropping (mostly passive)
- Possible when attacker has access to network traffic.
- Very dangerous when the victim is not using any additional security mechanism such as TLS, HTTPS. SSH etc.
Manipulation (mostly active)
- An active process in which attacker tries to manipulate traffic so that he can capture it.
- ARP poisoning enables these attacks.
Fake Access Points:
- A fake AP is a honeypot, which is a fake access point made to attract hackers and other wireless intruders in order to collect information about them.
- When a wireless client looks for a wireless connection, it can be lured into connecting to fake or rouge AP’s with lucrative names such as “free internet” etc.
- Once connected to the AP, the victim exposes his machine to the attacker, which can use vulnerabilities to attack services running on the victim.
- Also, one approach is to provide internet to the victim, and dumping all the traffic.
- Karmetasploit is an excellent metasploit module, designed for setting up fake AP’s and automatically exploiting them.
How does WEP work?
WEP uses secret keys to encrypt data. Both AP and the receiving stations must know the secret keys.
There are two kinds of WEP with keys of either 64bits or 128bits. The longer key gives a slightly higher level of security (but not as much as the larger number would imply). In fact the user keys are 40bits and 104bits long, the other 24bits in each case being taken up by a variable called the Initialization Vector (IV).
When a packet is to be sent it is encrypted using a combination of the IV and the secret key. The IV is different (in theory) for each packet, while the secret key is fixed. The resulting packet data looks like random data and therefore makes the original message unreadable to an outsider not knowing the key. The receiving station reverses the encryption process to retrieve the message in clear text.
What's wrong with WEP?
IV values can be reused
In fact the standard does not specify that the value needs to change at all. Reusing keys is a major cryptographic weakness in any security system.
IV length is too short
24 bit keys allow for around 16.7 million possibilities. Sounds a lot, but on a busy network this number can be achieved in a few hours. Reuse is then unavoidable.
Some manufacturers use ’random’ keys. This is not the best way to ensure against reuse. A better solution is to start with a key and increment by one for each subsequent key. Unfortunately many devices revert to the same value at start up and then follow the same sequence providing lots of duplicate values for hackers to work on.
Weak keys are susceptible to attack
Certain keys value combinations, ’Weak IVs’, do not produce sufficiently random data for the first few bytes. This is the basis of the highly publicized attacks on WEP and the reason that keys can be discovered.
Manufacturers often deliberately disallow Weak IV values. This is good in that it reduces the chances of a hacker capturing weak keys, but also has the effect of reducing the already limited key possibilities further, increasing the chance of reuse of keys.
Master keys are used directly
From a cryptographic point of view using master keys directly is not at all recommended. Master keys should only be used to generate other temporary keys. WEP is seriously flawed in this respect.
Key Management and updating is poorly provided for
Administration of WEP keys is not well designed and difficult to do on large networks. Users tend to change keys very infrequently which gives a potential hacker lots of time to collect enough packets to launch an attack.
Message integrity checking is ineffective
WEP does have a message integrity check but hackers can change messages and recompute a new value to match. This makes the checking ineffective against tampering.
What's New in WPA (Wi-Fi Protected Access)
WPA is wireless security with greater protection than WEP. Most wireless networks should use either WEP or WPA. WPA-PSK is not much more difficult to configure than the older WEP, but is not available on some older products. All computers, access points, and wireless adapters must use the same type of security. See your user manuals for configuration instructions.
WPA operates in either WPA-PSK mode (aka Pre-Shared Key or WPA-Personal) or WPA-802.1x mode (aka RADIUS or WPA-Enterprise). In the Personal mode, a pre-shared key or passphrase is used for authentication. In the Enterprise mode, which is more difficult to configure, the 802.1 x RADIUS servers and an Extensible Authentication Protocol (EAP) are used for authentication. The enhanced WPA2 uses Advanced Encryption Standard (AES) instead of Temporal Key Integrity Protocol (TKIP) to provide stronger encryption mechanism.
Advantages of WPA
- Provides extremely strong wireless security for the 2003 computing environment.
- Adds authentication to WEP's basic encryption.
- Has backward compatible WEP support for devices that are not upgraded.
- Integrates with RADIUS servers to allow administration, auditing, and logging.
Disadvantages of WPA
- Except when using with the preshared key (WPA-PSK), complicated setup is required, unsuitable for typical home users.
- Older firmware usually will not be upgraded to support it.
- Incompatible with older operating systems such as Windows 95.
- Greater performance overhead than WEP.
- Remains vulnerable to Denial of Service attacks.
Facts About WPA:
- To use WPA, all computers, access points, and wireless adapters must have WPA software.
- WPA was introduced in 2003. To run WPA between two computers both must have WPA software, and all access points and wireless adapters between them, as well. Equipment older than 2003 will often not be upgradable.
WPA has significant advantages over WEP:
- An encryption key differing in every packet. The TKIP (Temporal Key Integrity Protocol) mechanism shares a starting key between devices. Each device then changes their encryption key for every packet. It is extremely difficult for hackers to read messages — even if they've intercepted the data.
- Certificate Authentication (CA) can be used, blocking a hacker's access posing as a valid user.
- WPA computers will communicate with WEP encryption, if they cannot use WPA with a particular device.
- A Certificate Authority Server is part of the recommended configuration, to allow WPA computers assurance that the computers with whom they share keys are who they claim.
- Since WPA adds to packet size, transmission takes longer. The encryption and decryption are slower for devices using software, rather than dedicated WPA hardware.
The EAP types supported by WPA-Enterprise are
- EAP-TLS
- EAP-TTLS/MSCHAPv2
- PEAPv0/EAP-MSCHAPv2
- PEAPv1/EAP-GTC (Cisco-based implementation)
- EAP-SIM
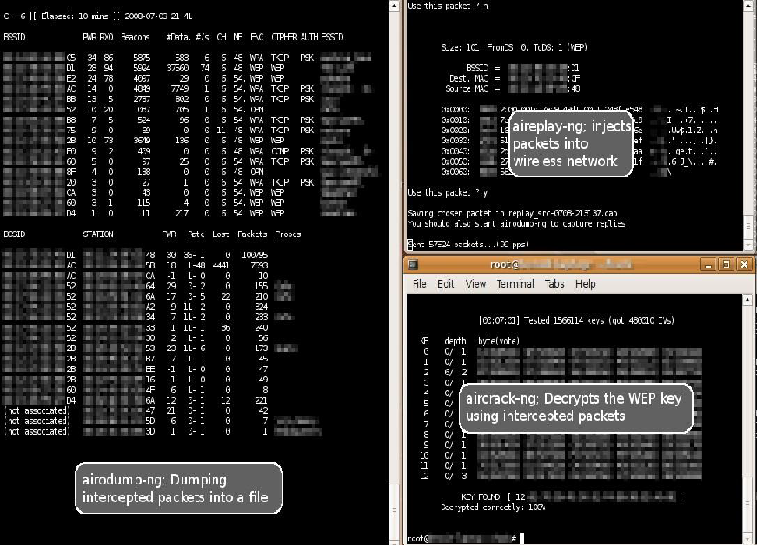
WEP Cracking:
For cracking WEP airmon-ng,airodump-ng and aircrack-ng package are used in linux based system.
WEP Cracking works in the following manner
- First, the wireless card is put to the monitoring mode, using which raw packets can be dumped.
- A lot of interesting packets are needed, so in a low volume network, packet injection is done to increase the interesting packet numbers.
- Once the required number of packets are achieved, the problems with the implementation of WEP are exploited, which is primarily with the implantation of the RC4 Algorithm to encrypt the packets.
ALSO:
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: