- Cisco Community
- Technology and Support
- Networking
- Switching
- C9300 802.1x EAP-MD5 for IP-Phones not working
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
C9300 802.1x EAP-MD5 for IP-Phones not working
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-25-2020 06:41 AM
Hi,
we have cisco C3560X-48P Switches in our branches and use Avaya IP-Phones for our call agents. All switchports are protected by 802.1x and our Avaya IP-Phones use EAP-MD5 with username and password to authenticat the phone in the voice subnet.
this is our port config:
interface GigabitEthernet0/1
description Avaya IP-Phone
switchport access vlan 10
switchport mode access
switchport voice vlan 2000
ip arp inspection limit rate 130 burst interval 2
no logging event link-status
authentication control-direction in
authentication event fail action authorize vlan 10
authentication event server dead action authorize vlan 10
authentication event no-response action authorize vlan 10
authentication event server alive action reinitialize
authentication host-mode multi-domain
authentication order dot1x
authentication priority dot1x
authentication port-control auto
authentication periodic
authentication timer reauthenticate server
authentication violation restrict
dot1x pae authenticator
dot1x timeout tx-period 1
no cdp enable
spanning-tree portfast
everything works well so far....
now we want to replace your c3560x switches with the new C9300-48UXM (IOS: 16.09.05) without change our IP-Phone Settings.
we use the same port config as we had on c3560x but the IP-Phones couldn't authenticate.
LLDP Neighbour Table is also empty and the c9300 switch send an error
Aug 25 15:33:00: %DOT1X-5-FAIL: Switch 1 R0/0: sessmgrd: Authentication failed for client (001b.4f30.97e3) with reason (No Response from Client) on Interface Tw1/0/1 AuditSessionID 1410D10A0000001C25C446DF
Aug 25 15:33:00: %SESSION_MGR-5-FAIL: Switch 1 R0/0: sessmgrd: Authorization failed or unapplied for client (001b.4f30.97e3) on Interface TwoGigabitEthernet1/0/1 AuditSessionID 1410D10A0000001C25C446DF. Failure Reason: VLAN Failure.
Switch-C9300-001#sh authentication sessions
Interface MAC Address Method Domain Status Fg Session ID
--------------------------------------------------------------------------------------------
Tw1/0/1 001b.4xxx.9xxx dot1x DATA Unauth 1410D10A0000001C25C446DF
if I made a span session and capture the traffic during the authentication, I can see a "EAP" Failure in Wireshark.
if I do not use 802.1x config on a switchport my phone working well.
could it be that the new c9300 does not support EAP-MD5 challenges or does anyone has an idea what i can try or what my problem is ?
many many thanks for your support
- Labels:
-
Catalyst 9000
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-08-2020 10:18 PM
Hi,
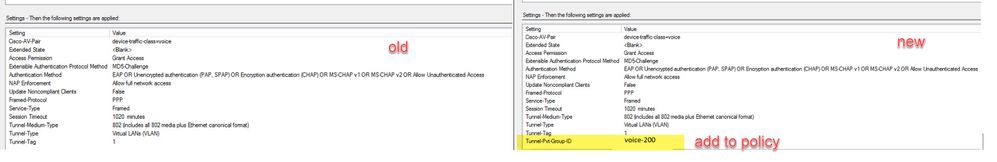
i try it with photo upload. I hope you can read the details on this picture.
left is my NPS policie for c3560x swiches and on the right side I add the "tunnel-pvt-group-id" with the voice-vlan.
right looks like it workt's for booth switche types. I have to do some tests in our lab... after vacation :-)
thanks a lot for your support.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-10-2020 07:46 PM
This is a solution to push the voice vlan.
You can also push the domain voice with following attribute:
cisco-av-pair = device-traffic-class=voice
Thanks
Francesco
PS: Please don't forget to rate and select as validated answer if this answered your question
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-29-2020 03:05 AM
hi, if you can see in my last post on the printscreen, we already send the domain in in "cisco-av-pair"
for my the only one solution is, if I add the "tunnel-pvt-group-id" with the voice-vlan name.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-29-2020 07:04 PM
Yes i saw it.
I'm not doing dot1x with NPS but I'm gonna try with 9300 switches and do some debugs when I'll get a 9300 available.
Thanks
Francesco
PS: Please don't forget to rate and select as validated answer if this answered your question
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-19-2021 04:54 PM
Hi Stefan:
Thank you for posting this screen shot. This is very helpful as to what settings I should configure for the Network Policy in Windows Network Policy Server. Similar to your setup, I am the network/server administrator of an organization that uses Avaya 9600 phones deployed in a Cisco Catalyst 9300 environment. I have been struggling to get my phones to authenticate via 802.1x. The PC that I connected to the phone authenticate successfully; however, the phones go into an unauthorized state.
Do you mind providing a quick run down as to how you have your phones configured in your Active Directory Server, as well as the network connection request policy and network policy itself. I am running into a brick wall and would appreciate any feedback on this.
Thank you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-27-2022 03:45 PM
Stefan,
Could you provide me with more details as far as what you did with the tunnel-pvt-group-id config you mentioned? I might be running into this problem as well. Do you have a print screen you can share? Thanks, -Matt
- « Previous
-
- 1
- 2
- Next »
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide