- Cisco Community
- Technology and Support
- Networking
- Switching
- Dual ISP without BGP and a firewall
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Dual ISP without BGP and a firewall
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-08-2012 01:27 AM - edited 03-07-2019 08:12 AM
Hey all so first post so forgive me if I miss something critical.
This has been doing my head in now for a couple of weeks and Im hoping to bounce it around in here for a bit of assistance.
Basically I have a customer who has two ISP circuits which I plan on plugging into a 2911. Now I have configured it like this document
http://www.blindhog.net/cisco-dual-internet-connections-without-bgp/
This bit I have working fine.
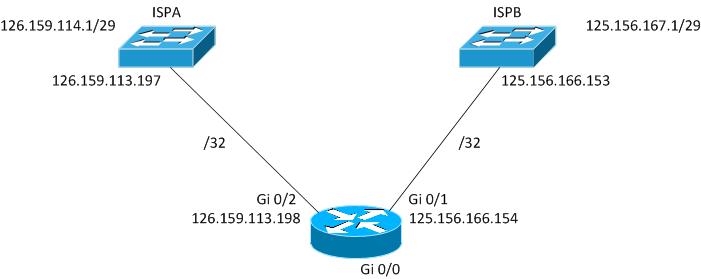
So here is my topolgy
Ok so onto the next bit
ISP B was originally plugged into an ASA5510. So on this I have a whole world on NAT and PAT translations for internal servers. My external interface on the ASA was the 125.156.166.154/32 address and I PAT for all internal going outbound. Static NATs are assigned to the /29. So my new topology now looks like this.
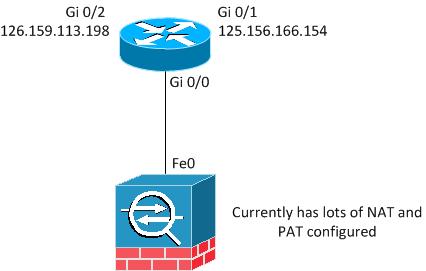
What I need to know here is how do I get from firewall to router. If I asssign another /32 between fe0 and gi0/0 do I not end up doing double nat? The end user also manages the firewall at the moment and I dont want to have to do the translations on the router. Is this even possible? I have search the internet for many many hours now trying to find an example but have failed miserably.
But I only want my existing NAT through ISP B. I am using Policy Based Routing on these as I have specific traffic I need to go through ISP A.
Appreciate everyones feedback as Im now numb trying to find the solution.
- Labels:
-
Other Switching
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-08-2012 08:36 AM
I think the only way you'll avoid doing NAT on the router itself is if you can use one of your /29 addresses as the new outbound PAT address on your ASA. Either way, you're going to have to create a new /30 range between the ASA and the 2911, and the 2911 will need to have routes to your /29 pointing back to the ASA.
If you don't have an extra address, you'll have to do a PAT on the router interface.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide