- Cisco Community
- Technology and Support
- Collaboration
- TelePresence and Video Infrastructure
- Hi Acevirgil Thanks.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Expressway C and E dual NIC static
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-26-2017 06:59 AM - edited 03-18-2019 01:03 PM
Hi team,
Have you ever done this cenario of configuration with expressway C and E integrated with Cisco BE7K with cucm, cuc, imp in the version 11.5?
Does anybody knows if the palo alto firewalls support expressway with dual nic and dmz?
Best regards,
Daniel Sobrinho
- Labels:
-
Room Endpoints
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-26-2017 05:14 PM
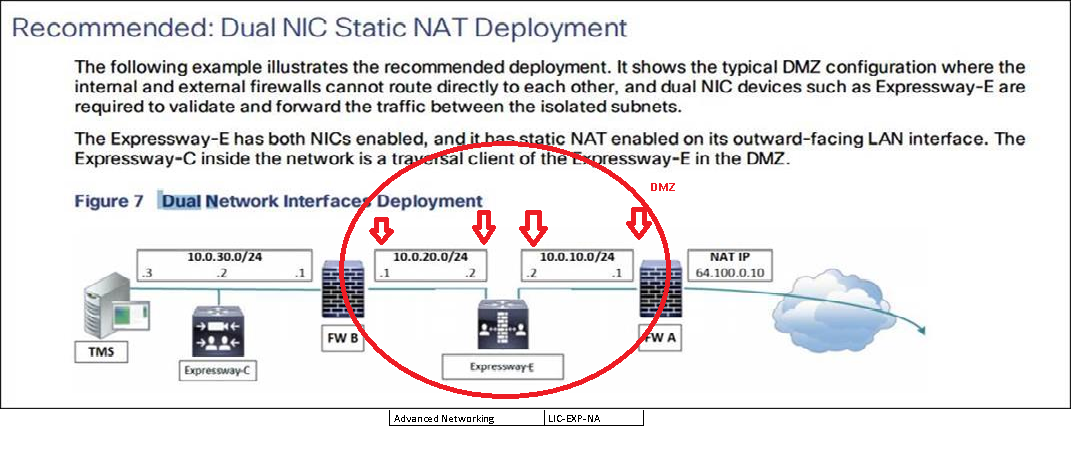
The Palo Alto Firewall can be used in the deployement you show above, with Expressway-E using dual NIC, however the firewall should only know about the NIC used as the "External" interface. The NIC used as the "Internal" interface is invisible for the firewall.
You really don`t need to use 2 firewalls (FWA ans FWB), with one firewall is fine, the External NIC needs to be in the DMZ with Static NAT (just in case that you were concerned about your Palo Alto FW to use 2 of its interfaces).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-27-2017 05:35 AM
Hi Elias,
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-27-2017 06:29 AM
My pleasure to help.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-23-2017 05:15 PM
Hi Elias,
If I have one ASA with one DMZ interface ? I'll put one interface in DMZ and the other interface in internal ? and do static nat for the one on DMZ and configure all the communications to EXPc to the ip add of the internal EXPe interface ?
Is it ok or it is recommended to have EXPe with dual nic and to connect each nic to a different DMZ of the fw ?
That I'm using now the option of 3-port firewall with one EXPe interface with static nat and EXPc is talking with the public ip of the EXPe. but I didn't do nat reflection. I don't understand how ?
Also I open the required ports between EXPc and the DMZ ip of the EXPe and I think I should open between EXPc and EXPe public ip address
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-24-2017 09:15 PM
Hi,
When using a 3-Port firewall, the Exp-E should use only 1 NIC, with static NAT. See atached screenshot. Static NAT needs to be "On" in the Exp-C NIC.
NAT Reflection is a simple 1:1 NAT (Also known as NAT Loopback), which should allow the Private IP address of the Exp-C to communicate with the NAT IP address of the Exp-E. Check out the below guide in page 71.
http://www.cisco.com/c/dam/en/us/td/docs/telepresence/infrastructure/vcs/config_guide/X8-9/Cisco-VCS-Basic-Configuration-Control-with-Expressway-Deployment-Guide-X8-9.pdf
If NAT reflection is in place, then the Exp-C should be configured with the NAT IP address of the Exp-E in the Traversal Client Zone with port TCP 7001 for SIP (the most common TCP port) and UDP port 6001 for H323 (also the most common). This ports should be open in the FW in order to allow the zone to come up.
Was this of help? Let me know.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-29-2018 07:55 AM - edited 08-29-2018 08:01 AM
Hi Alias,
So The LAN1 of Expressway E can be in internal subnet not DMZ. So could you explain how the LAN 1 is invisible to the FW??
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-27-2017 03:31 AM
Hello,
There should be no problem using Palo Alto FW with the Expressway-E/VCS-E dual nic deployment. We have already deployed Expressway-E using Palo Alto and other firewalls like Cisco ASA, Juniper, Fortinet and so far it works fine.
regards,
Acevirgil
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-27-2017 05:35 AM
Hi Acevirgil
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-18-2019 10:55 PM
Dear team ,
we have single NIC Deployment - Expressway E
For example exp c has ip address 10.0.0.18 and EXP E has 10.0.0.19
and we have nated EXP E with Public IP 1.1.1.1
so in this case what you have configured in Fortgate firewall and both are belongs to inside interface .
@Acevirgil de Ocampo wrote:Hello,
There should be no problem using Palo Alto FW with the Expressway-E/VCS-E dual nic deployment. We have already deployed Expressway-E using Palo Alto and other firewalls like Cisco ASA, Juniper, Fortinet and so far it works fine.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide






