- Cisco Community
- Technology and Support
- Security
- VPN
- Community Ask Me Anything- Configuration, Troubleshooting and Best Practices: AnyConnect Remote Acce...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-03-2020
05:28 PM
- last edited on
04-27-2020
09:00 AM
by
Hilda Arteaga
![]()
| Español | Português | Français | Русский | 日本語 | 简体中文 |
This event continues the conversation of our recent Community Ask Me Anything event "Secure Remote Workers".
Here’s your chance to discuss more about the configuration, troubleshooting and best practices for AnyConnect secure mobility client on a Cisco Adaptive Security Appliances (ASA) and Firepower Threat Defense (FTD) and its integration with other Cisco security portfolio devices and technologies like ISE and Duo.
This session provides an opportunity to learn and ask questions about various aspects of AnyConnect implementation (using SSL and Ikev2) including (but not limited to) emergency licenses, configuration, deployment and troubleshooting AnyConnect that provides the security necessary to help ensure that your organization is safe and protected in such critical situation.
To participate in this event, please use the ![]() button below to ask your questions
button below to ask your questions
Ask questions from Monday 6 to Friday, April 17, 2020
 Dinesh Moudgil is a High Touch Technical Support (HTTS) Engineer with the Security team at Cisco. He has been working on Cisco technologies for more than 6 years focusing on Cisco Next Generation Firewalls, Intrusion Prevention Systems, Identity Management and Access Control (AAA) and VPNs. He holds a CCNP, CCDP and CCIE #58881 certifications, and multiple vendors certifications such as ACE, PCNSE and VCP.
Dinesh Moudgil is a High Touch Technical Support (HTTS) Engineer with the Security team at Cisco. He has been working on Cisco technologies for more than 6 years focusing on Cisco Next Generation Firewalls, Intrusion Prevention Systems, Identity Management and Access Control (AAA) and VPNs. He holds a CCNP, CCDP and CCIE #58881 certifications, and multiple vendors certifications such as ACE, PCNSE and VCP. Pulkit Saxena works as High Touch Technical Support (HTTS) Engineer in Security Domain with Cisco bring nearly 7 years of experience in the industry to the team. He has hands on experience with multiple firewalls, different VPN solutions, AAA and Next Generation IPS along with delivering multiple trainings. Pulkit holds certifications from multiple vendors, namely Cisco and Juniper, (CCIE Security and JNCIA).
Pulkit Saxena works as High Touch Technical Support (HTTS) Engineer in Security Domain with Cisco bring nearly 7 years of experience in the industry to the team. He has hands on experience with multiple firewalls, different VPN solutions, AAA and Next Generation IPS along with delivering multiple trainings. Pulkit holds certifications from multiple vendors, namely Cisco and Juniper, (CCIE Security and JNCIA). Jason Grudier is the Technical leader on the VPN TAC team in Raleigh, NC. He has been working for Cisco on the VPN team for six years. Prior to joining the team, he was a network engineer at Labcorp. He works primarily with AnyConnect troubleshooting and configuration across all Cisco platforms as well as DMVPN, GETVPN, Radius, LDAP and Certificate authentications.
Jason Grudier is the Technical leader on the VPN TAC team in Raleigh, NC. He has been working for Cisco on the VPN team for six years. Prior to joining the team, he was a network engineer at Labcorp. He works primarily with AnyConnect troubleshooting and configuration across all Cisco platforms as well as DMVPN, GETVPN, Radius, LDAP and Certificate authentications. Gustavo Medina is a Systems Sales Engineer with the Enterprise Networking Sales team. He has more than 10 years of experience in security and enterprise networking. In his career he has focused on different tasks from technical escalations and partner adoption to the revision of Cisco Certification evaluations. Gustavo holds a CCNA, CCNP CCSI, and a CCIE in security (#51487).
Gustavo Medina is a Systems Sales Engineer with the Enterprise Networking Sales team. He has more than 10 years of experience in security and enterprise networking. In his career he has focused on different tasks from technical escalations and partner adoption to the revision of Cisco Certification evaluations. Gustavo holds a CCNA, CCNP CCSI, and a CCIE in security (#51487).By posting a question on this event you're giving permission to be translated in all languages we have in the community.
**Helpful votes Encourage Participation! **
Please be sure to rate the Answers to Questions
Solved! Go to Solution.
- Labels:
-
AnyConnect
-
Other VPN Topics
- Adaptive Security appliance
- AMA
- Annyconnect integration
- anyconnect
- Anyconnect Ikev2
- anyconnect posture
- anyconnect vpn
- asa
- ask me anything
- cisco
- Cisco Community
- cisco tac
- classic licensing
- coronavirus
- COVID 19
- Dinesh Moudgil
- Dynamic Access Policy
- emergency
- firepower
- firepower forum vent
- FirePOWER Threat Defense
- forum event
- FTD
- Gustavo Medina
- Host scan
- Jason Grudier
- license
- nam
- ogs
- Optimal Gateway Selection
- pandemic
- Pulkit Saxena
- remote access vpn
- secure remote worker
- security
- smart licensing
- ssl vpn
- tnd
- trusted network detection
- vpn
- wfo
- working from home
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2020 01:53 AM
I checked with the product team as well, currently we do not have any roadmap for L2TP addition in upcoming releases of firepower as well.
So anyconnect client is the way to go. :)
-
Pulkit
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2020 12:36 AM
Hi,
Could you please confirm which method we should use to generate the csr and upload it to the FTD firewall for Anyconnect users authentication.
Objects>PKI>Cert Enrollment or using Open SSL?
Thanks
Basavaraj
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2020 02:56 AM
I believe you are looking for server authentication which is mandatory as per SSL handshake, so when an anyconnect user connects, FTD needs to present its certificate which the end client will check against its trusted CA list.
Here is a link which can help you with the configuration :
https://www.cisco.com/c/en/us/support/docs/network-management/remote-access/212424-anyconnect-remote-access-vpn-configurati.html
To answer your question, we can opt for any method, generating CSR on FTD, or using open SSL, for the second one, we can import the complete PKCS12 once ready.
Now in case you are looking for user authentication using certificate, FTD only needs to have CA certificate in its database, not the user certificate.
Hope this helped.
-
Pulkit
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2020 05:18 AM
In my case, I'm looking for the certificate authentication for the domain users, anyone connecting from personal devices they should not get VPN access. only corporate machines should be able to connect to VPN
if I just import the ROOT CA Certificate of my internal CA server into my FTD and which certificate I have to install on the client-side? any specific certificate template we have to use when creating certificate for the users
Thanks
Basavaraj
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-06-2020 04:03 AM
So the ask here is to have client authentication as well using certificates, for which you are correct. You just need to have the root CA certificate of the clients on FTD.
The clients needs to provide it's ID certificate to the FTD while SSL negotiation, and FTD should be having the CA certificate for the same.
-
Pulkit
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2020 04:07 AM
Hi Dinesh,Pulkit,Jason,Gustavo,
Thanks for hosting this Q&A session, I am going to list some questions that comes to mind at the moment
- Can you describe the process to integrate ISE posture profile into FTD? I am familiar with ASA but I haven't tried yet with FTD (managed via FMC)
- What are pro and cons of having sysopt connection permit-vpn enabled in FTD? what is the recommended best practice in either case? (I understand that without sysopt connection permit-vpn then all access needs to be regulated via the ACP)
- Is CoA supported with FTD as much as with ASA? question especially relevant with ISE posture
- Is there an Anyconnect profile editor built in FMC ? in case not what is preferred? Anyconnect standalone editors or ISE profile editor?
- Can you provide a sample to automate a configuration push for FTDs managed via FMC? Currently we have some scripts in ASA with parameters and we standardize our configurations but in FTD since there is no option to access the CLI besides Flexconfig exceptions I assume that using API objects call will be necessary, just I would like to have a starting sample
- (this is more of a generic FTD/FMC question) In order to quickly troubleshoot access in ASA we use ASDM that gives us a quick overview of the traffic being processed, in FMC I know that connection events cannot offer the same level of information for some reasons: one is the delay in the connection events and the load on FMC with multiple troubleshooting engineers, also connection events comes out of the snort processing backend if I am not mistaken so interface ACL denies goes through syslog and hence connection events may not provide that level of information required : What is best practice to analyze quickly access logs for ACP rules beween ACL interface drops and DPI drops?
Thank you all, really.
PS: To not mix up you can refer the answer with the number of the queston.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-06-2020 05:29 AM
Hi Giovanni,
Here are answers to your queries:
1. Here is a document you can refer to understand the flow and configuration steps required for ISE posture on FTD
https://www.cisco.com/c/en/us/support/docs/security/identity-services-engine/215236-ise-posture-over-anyconnect-remote-acces.html
2. The option to select Bypass Access Control policy for decrypted traffic would be recommended when we don´t want to inspect the VPN traffic through the Access Control Policy. Thus, the traffic will be just forwarded to the destination without any deep inspection from the FTD. To have this feature enabled or not, that depends on what your security requirements are and of the level of trust that you have on the remote access VPN users. If you don´t trust the traffic initiated from remote access VPN users, it is advised to apply deep inspection on the traffic generated from them.
For the record, this command is disabled by default on FTD and enabled by default on the ASA.
Please note that VPN Filter ACL and authorization ACL downloaded from AAA server are still applied to VPN traffic.
Use case of having "Bypass Access Control policy for decrypted traffic (sysopt permit-vpn)" unchecked is if you want to allow the u-turning of Anyconnect user traffic to be able to access internet via FTD or perhaps access internal resources. With this feature being disabled, ACP checks will be performed and you can leverage features like URL filtering to restrict Anyconnect user initiated traffic.
3. Yes, RADIUS CoA is indeed supported on FTD from 6.3.0 version onwards and fully supported with newer versions.
4. You can create an AnyConnect client profile using the AnyConnect Profile Editor. This editor is a GUI-based configuration tool that is available as part of the AnyConnect software package. It is an independent program that you run outside of the Firepower Management Center.
For more information about AnyConnect Profile Editor, please refer:
https://www.cisco.com/c/en/us/td/docs/security/vpn_client/anyconnect/anyconnect48/administration/guide/b_AnyConnect_Administrator_Guide_4-8/anyconnect-profile-editor.html
5. You can leverage the API Explorer as it provides a limited interface for the REST API as well as giving a view of the abilities of the REST API.
https://<management_center_IP_or_name>:<https_port>/api/api-explorer
Here are few links to get you started with programming firepower using FMC APIs
https://blogs.cisco.com/security/how-to-get-started-on-programming-firepower-using-fmc-apis
https://www.cisco.com/c/en/us/td/docs/security/firepower/623/api/REST/Firepower_Management_Center_REST_API_Quick_Start_Guide_623/Objects_in_the_REST_API.html#concept_xh5_lt3_bcb
Here are some non Cisco links that might be helpful:
https://www.youtube.com/watch?v=a2DNeRxnnkA
https://www.youtube.com/watch?v=iTfmLk3kwdg
6. TAC uses CLI predominantly along with FMC GUI to troubleshoot issues related to ACP rules.
You can either use packet capture option at LINA CLI, similar to what is used on a traditional ASA
or
you can use "system support firewall-engine-debug" under FTD clish to confirm whether traffic flow is evaluated against the proper Access Control rule.
Here is a document for your reference:
https://www.cisco.com/c/en/us/support/docs/security/firepower-ngfw/212474-working-with-firepower-threat-defense-f.html#anc13
Regards,
Dinesh Moudgil
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-06-2020 11:33 PM
That's a question from Cisco customer:
How to ensure that the threat of the user's computer does not affect the server, when the user's computer uses VPN
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-07-2020 05:50 AM
We can perform some pre-login checks to ensure that the client machine is trusted and can be allowed to connect.
Possible options are posturing, DAP, CSD hostscan. Check out below helpful links :
https://www.cisco.com/c/en/us/support/docs/security/asa-5500-x-series-firewalls/200238-ASA-VPN-posture-with-CSD-DAP-and-AnyCon.html
https://community.cisco.com/t5/security-documents/how-to-configure-posture-with-anyconnect-compliance-module-and/ta-p/3647768
https://www.cisco.com/c/en/us/td/docs/security/vpn_client/anyconnect/anyconnect40/administration/guide/b_AnyConnect_Administrator_Guide_4-0/configure-posture.html
https://www.cisco.com/c/en/us/td/docs/security/asa/asa98/asdm78/vpn/asdm-78-vpn-config/vpn-asdm-dap.html
Once the user is connected on basis of above checks and is compliant, we ideally believe it to be a trusted user. In addition we can only allow relevant traffic to come to ASA or all traffic tunnelled using the split tunnel option :
https://www.cisco.com/c/en/us/support/docs/security/asa-5500-x-series-next-generation-firewalls/100936-asa8x-split-tunnel-anyconnect-config.html
Apart from this, if a user is sending excessive amount of traffic or has incomplete connections once connected, then this will have a specific troubleshooting depending upon the issue. However your primary concern can be taken care by the pre-login checks that I have mentioned.
-
Pulkit
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-07-2020 06:46 AM
Hi Yanli,
In addition to what Pulkit already mentioned, some companies use Always-On which prevents access to Internet resources when the computer is not on a trusted network, unless a VPN session is active. Enforcing the VPN to always be on in this situation protects the computer from security threats.
For companies that to do not enforce Always-On, besides the posture checks already mentioned + 2FA like DUO (to ensure only authorized people are using the VPN) we must add additional protection to the remote users as threat actors are taking advantage of the increase of unprotected remote workers to launch different campaigns. You can read our TALOS blog for more:
https://blog.talosintelligence.com/2020/03/covid-19-pandemic-threats.html
With Cisco Umbrella you can protect users from malicious Internet destinations even when they are not connected to the VPN at the DNS layer. Because it is delivered from the cloud, Umbrella makes it easy to protect users everywhere in minutes.
Also, we have the last line of defense which is Cisco Advanced Malware Protection (AMP) for Endpoints. This technology prevents breaches and blocks malware at the point of entry as well as detects, contains and remediates advanced threats if they evade the frontline of defense.
Regards,
Gustavo
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-07-2020 04:20 AM
I want to ask how to allow users communicate voice through skype for business or cisco jabber Anyconnect Remote Access VPN on ASA, and is below commends safe to be done from security prospective. also how I can make this internal communications monitored from our SIEM solution.
Enter the same-security-traffic command in order to make the FW as a HUB. And You’ll need to configure a nat rule for nat (outside , outside) for the pool address space to reach each other.
ciscoasa(config)#same-security-traffic permit intra-interfacePlease note that this command allows traffic to enter and exit the same interface, which is disabled by default for security.nat(outside,outside) source static “address pool obj” “address pool obj” dest static “address pool obj” “address pool obj” no-proxy-arp – route-lookupAnd be place towards the top of your nat rules.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-07-2020 06:37 AM
Hello ahmedmohsen56,
This is the only way to set up hairpining on the ASA to allow AnyConnect clients to talk to other AnyConnect clients. I would not consider this a great security threat, but it all depends on the needs of your company, and only you can make those decisions.
From the command reference:
https://www.cisco.com/c/en/us/td/docs/security/asa/asa-command-reference/S/cmdref3/s1.html
The same-security-traffic intra-interface command lets traffic enter and exit the same interface, which is normally not allowed. This feature might be useful for VPN traffic that enters an interface, but is then routed out the same interface. The VPN traffic might be unencrypted in this case, or it might be reencrypted for another VPN connection. For example, if you have a hub and spoke VPN network, where the ASA is the hub, and remote VPN networks are spokes, for one spoke to communicate with another spoke, traffic must go into the ASA and then out again to the other spoke.

Note![]() All traffic allowed by the same-security-traffic intra-interface command is still subject to firewall rules. Be careful not to create an asymmetric routing situation that can cause return traffic not to traverse the ASA.
All traffic allowed by the same-security-traffic intra-interface command is still subject to firewall rules. Be careful not to create an asymmetric routing situation that can cause return traffic not to traverse the ASA.
What is it that your are trying to monitor via SIEM solution?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-07-2020 07:26 AM
Hello Ahmed and Jason,
Couple of comments:
- The "nat (outside , outside) for the pool address space to reach each other" you mentioned is only required if there is already a NAT for Public Internet on a Stick. If using split-tunnel then this is not needed.
https://www.cisco.com/c/en/us/support/docs/security/asa-5500-x-series-next-generation-firewalls/100918-asa-sslvpn-00.html#anc10 - If using split tunnel, no manual NAT is required in order to allow bidirectional communication unless there is a NAT rule that affects this traffic configured. However the Anyconnect VPN Pool must be included on the Split-Tunnel ACL.
https://www.cisco.com/c/en/us/support/docs/security/asa-5500-x-series-next-generation-firewalls/100918-asa-sslvpn-00.html#anc14 - From a security-perspective same-security-traffic intra-interface should not be a big concern as traffic will still be subject to FW rules but of course you will always want to have additional protection for your remote users like DUO, Umbrella and/or AMP4E.
-
You can definitely monitor these communications on your SIEM the same way you are doing for other traffic. For better visibility of what your Remote Users are doing you can use Stealthwatch Enterprise or Stealthwatch Cloud as shown in these videos:
https://cs.co/SWE-RemoteMonitoring
https://cs.co/SWC-RemoteMonitoring
*We could even get to workload/app granularity with Tetration but that's a conversation for another day :)
Regards,
Gustavo
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-07-2020 04:49 AM
Hello,
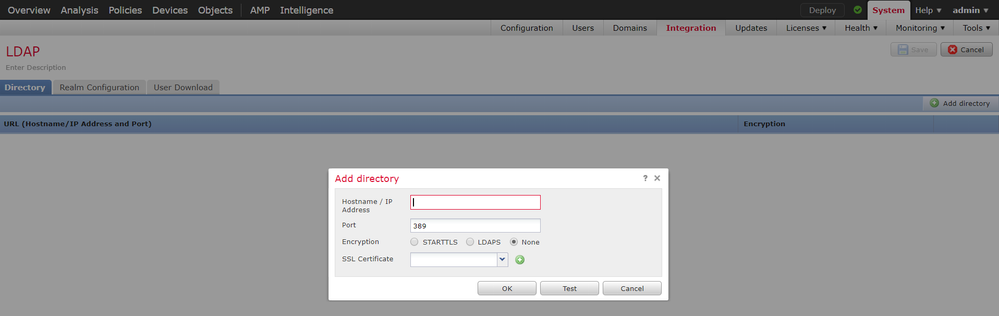
I configure the Remote VPN with realms on the FTD via FMC. When I try to connect with AnyConnect I take the error "Login error".
Below is debug output from ldap 255 and webvpn anyconnect 127:
ldap_client_server_add: Add server:0.0.0.0, group=4
ldap_client_server_unlock: Free server:0.0.0.0, group=4
[12] Session Start
[12] New request Session, context 0x00002b5de5d453b0, reqType = Authentication
[12] Fiber started
[12] Failed to convert ip address 0.0.0.0
[12] Fiber exit Tx=0 bytes Rx=0 bytes, status=-3
[12] Session End
Thanks for your help
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-07-2020 06:04 AM
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide