- Cisco Community
- Technology and Support
- Wireless - Mobility
- Wireless
- Re: 5520 WLC Redundancy Failure Event
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
5520 WLC Redundancy Failure Event
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-25-2023 02:56 AM
Hi,
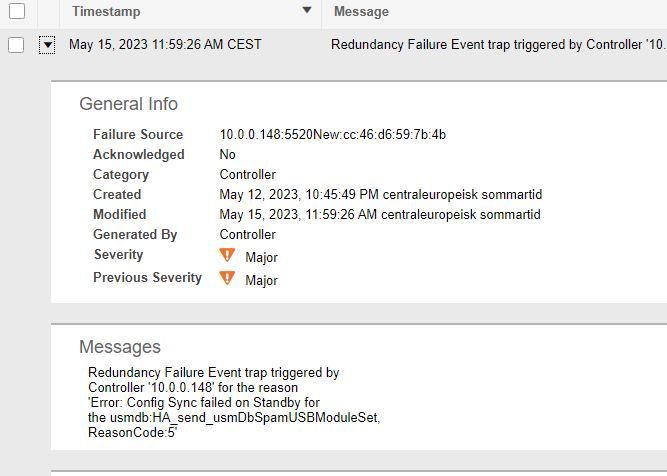
I have two 5520 in SSO mode and i see a message on Prime:
"Redundancy Failure Event trap triggered by
Controller 'x.x.x.x' for the reason
'Error: Config Sync failed on Standby for
the usmdb:HA_send_usmDbSpamUSBModuleSet,
ReasonCode:5'"
When i check the 5520 CLI i see this:
(Cisco Controller) >show redundancy config-sync statistics
Config Sync Counters........
--------------------------------------------------------------
Usmdb functions sent for sync...............................: 2394325
Failed sync for usmdb sync..................................: 14
UsmDbs failed:
--------------------------------------------------------------
1. UsmDb:HA_send_usmDbSpamUSBModuleSet, ErrType:Apply Config failed on Standby, Reason:5, TStamp:2023-Apr-06 09:49:39
2. UsmDb:HA_send_usmDbSpamUSBModuleSet, ErrType:Apply Config failed on Standby, Reason:5, TStamp:2023-Apr-06 09:49:07
3. UsmDb:HA_send_usmDbSpamUSBModuleOverrideSet, ErrType:Apply Config failed on Standby, Reason:5, TStamp:2023-Apr-06 09:49:07
4. UsmDb:HA_send_usmDbSpamUSBModuleSet, ErrType:Apply Config failed on Standby, Reason:8, TStamp:2023-Mar-06 16:01:44
5. UsmDb:HA_send_usmDbSpamUSBModuleOverrideSet, ErrType:Apply Config failed on Standby, Reason:2, TStamp:2023-Mar-06 16:01:44
6. UsmDb:HA_send_usmDbSpamUSBModuleOverrideSet, ErrType:Apply Config failed on Standby, Reason:5, TStamp:2023-Jan-23 09:13:12
7. UsmDb:HA_send_usmDbSpamUSBModuleSet, ErrType:Apply Config failed on Standby, Reason:5, TStamp:2023-Jan-23 08:29:07
8. UsmDb:HA_send_usmDbSpamUSBModuleOverrideSet, ErrType:Apply Config failed on Standby, Reason:5, TStamp:2023-Jan-23 08:29:07
9. UsmDb:HA_send_usmDbSpamUSBModuleSet, ErrType:Apply Config failed on Standby, Reason:8, TStamp:2023-Jan-09 09:26:41
10. UsmDb:HA_send_usmDbSpamUSBModuleOverrideSet, ErrType:Apply Config failed on Standby, Reason:2, TStamp:2023-Jan-09 09:26:41
--------------------------------------------------------------We are running software version 8.10.181.3
Is there any bug in this version that causes this problem?
Does this problem impact the failover process if it would happen?
- Labels:
-
Wireless LAN Controller
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-25-2023 03:24 AM
- Could be a bug , check redundancy status with : show redundancy summary
You may have a go with https://software.cisco.com/download/home/286284738/type/280926587/release/8.10.183.0 , and check if the problem remains in place or not ,
M.
-- Each morning when I wake up and look into the mirror I always say ' Why am I so brilliant ? '
When the mirror will then always repond to me with ' The only thing that exceeds your brilliance is your beauty! '
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-25-2023 03:53 AM
Any reason why the controller is loaded with a "special release" firmware?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-25-2023 04:12 AM
We are using this version because it was the only working version at the time it was released. We had no problem since then.
But now i got this message!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-25-2023 04:20 AM
>...But now i got this message!
- Inherent bugs may popup under the 'just circumstances' (...) or for instance there could be a sort for resource exhaustion , then rebooting (both) could help ; both factors are an even more argument to go for latest or a stable release : https://software.cisco.com/download/home/286284738/type/280926587/release/8.10.183.0
M.
-- Each morning when I wake up and look into the mirror I always say ' Why am I so brilliant ? '
When the mirror will then always repond to me with ' The only thing that exceeds your brilliance is your beauty! '
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-25-2023 07:05 AM
So, if this is a bug, would it impact the failover process in case a failover happens?
If the answer is yes, what would the impact be?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-25-2023 07:39 AM
- That is very difficult to determine, as stated verify current health of the HA SSO setup with : show redundancy summary , avoiding such questions can be achieved by upgrading , as I mentioned earlier.
M.
-- Each morning when I wake up and look into the mirror I always say ' Why am I so brilliant ? '
When the mirror will then always repond to me with ' The only thing that exceeds your brilliance is your beauty! '
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-26-2023 12:29 AM
This is "show redundancy summary " from the management interface
(Cisco Controller) >show redundancy summary
Redundancy Mode = SSO ENABLED
Local State = ACTIVE
Peer State = STANDBY HOT
Unit = Secondary (Inherited AP License Count = 1500)
Unit ID = CC:46:D6:FC:A6:E9
Redundancy State = SSO
Mobility MAC = CC:46:D6:59:7B:4B
Redundancy Port = UP
BulkSync Status = Complete
Link Encryption = ENABLED
Average Redundancy Peer Reachability Latency = 245 Micro Seconds
Average Management Gateway Reachability Latency = 383 Micro Seconds
Here is the active node:
show redundancy summary
Redundancy Mode = SSO ENABLED
Local State = ACTIVE
Peer State = STANDBY HOT
Unit = Secondary (Inherited AP License Count = 1500)
Unit ID = CC:46:D6:FC:A6:E9
Redundancy State = SSO
Mobility MAC = CC:46:D6:59:7B:4B
Redundancy Port = UP
BulkSync Status = Complete
Link Encryption = ENABLED
Average Redundancy Peer Reachability Latency = 233 Micro Seconds
Average Management Gateway Reachability Latency = 499 Micro Seconds
Here is the hot standby node:
(Cisco Controller-Standby) >show redundancy summary
Redundancy Mode = SSO ENABLED
Local State = STANDBY HOT
Peer State = ACTIVE
Unit = Primary
Unit ID = CC:46:D6:59:7B:4B
Redundancy State = SSO
Mobility MAC = CC:46:D6:59:7B:4B
Redundancy Port = UP
Link Encryption = ENABLED
Average Redundancy Peer Reachability Latency = 249 Micro Seconds
Average Management Gateway Reachability Latency = 618 Micro Seconds
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-26-2023 01:02 AM
- Looks ok for the moment and or it seems that failovers can work correctly ,
M.
-- Each morning when I wake up and look into the mirror I always say ' Why am I so brilliant ? '
When the mirror will then always repond to me with ' The only thing that exceeds your brilliance is your beauty! '
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-17-2023 07:00 AM
Agreed looks like failover will work but risk of some config loss due to sync errors.
That special version only had limited supported as an interim release so you should be upgrading to the TAC recommended release 8.10.185.0 (as per below) regardless to make sure you resolve known bugs and have a release which TAC will support.
If you still see the error after upgrading you can open a TAC case so they can analyse although a fix is unlikely at this point in the AireOS lifecycle. At best they could offer a workaround.
Please click Helpful if this post helped you and Select as Solution (drop down menu at top right of this reply) if this answered your query.
------------------------------
TAC recommended codes for AireOS WLC's and TAC recommended codes for 9800 WLC's
Best Practices for AireOS WLC's, Best Practices for 9800 WLC's and Cisco Wireless compatibility matrix
Check your 9800 WLC config with Wireless Config Analyzer using "show tech wireless" output or "config paging disable" then "show run-config" output on AireOS and use Wireless Debug Analyzer to analyze your WLC client debugs
Field Notice: FN63942 APs and WLCs Fail to Create CAPWAP Connections Due to Certificate Expiration
Field Notice: FN72424 Later Versions of WiFi 6 APs Fail to Join WLC - Software Upgrade Required
Field Notice: FN72524 IOS APs stuck in downloading state after 4 Dec 2022 due to Certificate Expired
- Fixed in 8.10.196.0, latest 9800 releases, 8.5.182.12 (8.5.182.13 for 3504) and 8.5.182.109 (IRCM, 8.5.182.111 for 3504)
Field Notice: FN70479 AP Fails to Join or Joins with 1 Radio due to Country Mismatch, RMA needed
How to avoid boot loop due to corrupted image on Wave 2 and Catalyst 11ax Access Points (CSCvx32806)
Field Notice: FN74035 - Wave2 APs DFS May Not Detect Radar After Channel Availability Check Time
Leo's list of bugs affecting 2800/3800/4800/1560 APs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-18-2023 02:56 AM
I did restart both (one at a time) and it went with no problems. But then they contiued to send that message:
So a service window to upgrade them should be done shortly!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide



