- Cisco Community
- Technology and Support
- Collaboration
- Unified Communications Infrastructure
- Clustered Expressway Edge using FQDN of Cluster as Common Name in CSR
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Clustered Expressway Edge using FQDN of Cluster as Common Name in CSR
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-20-2020 03:54 PM - edited 07-20-2020 03:56 PM
Hi all,
Kindly need your help
currently, I have set up clustered expressway edge for Jabber MRA as below
cluster1.domain.com
- edge1.domain.com
- edge2.domain.com
- edge3.domain.com
My question is
- If I use FQDN of Cluster as Common Name do I need to generate the certificate on each expressway edge node?
- Whether the CSR will look like as table below?
| Expressway Edge | Common Name | SAN |
| This CSR generated on edge1.domain.com | cluster1.domain.com | edge1.domain.com edge2.domain.com edge3.domain.com collab-edge.domain.com cluster1.domain.com |
| This CSR generated on edge2.domain.com | cluster1.domain.com | edge1.domain.com edge2.domain.com edge3.domain.com collab-edge.domain.com cluster1.domain.com |
| This CSR generated on edge3.domain.com | cluster1.domain.com | edge1.domain.com edge2.domain.com edge3.domain.com collab-edge.domain.com cluster1.domain.com |
Nanda Nurhadyan
- Labels:
-
Unified Communications
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-21-2020 12:10 AM
I would say that you would only need to generate the certificate on the master node in your cluster with the content of the SAN as you have in your list. Then you’d upload it to each cluster node with root CA certs.

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-21-2020 01:33 AM
The above will be the best option.
you can also refer the below link.
https://video.cisco.com/video/5809964179001

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-28-2020 07:08 AM
Looking for your help Nithin- in the process of building clusters EXP-C/E where all nodes are still standalone. According to the cisco official video above, CN is the FQDN of the expressway while the documentation says the CN should be the FQDN of the cluster. Please advise.
If the Expressway is not clustered:
Subject Common Name = FQDN of Expressway
Subject Alternate Names = leave blank*
If the Expressway is clustered, with individual certificates per Expressway:
Subject Common Name = FQDN of cluster
Subject Alternate Name = FQDN of Expressway peer, FQDN of cluster*
Austin
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2020 08:43 PM
Hi Roger,
So I just need to generate the CSR from master node and upload on each node in the cluster that should work?
Because I worried that the private key from each node is different then if I only generate CSR from master node and get sign from Public CA, when I upload on each node in the cluster it will not work because the private key is different each nodes.
Nanda Nurhadyan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2020 10:07 PM
You can copy the private key from the first sever and use it in the reaming.
follow the below steps to copy the private key from primary.
- login as root.
- go to /tandberg/persistent/certs
- cat privkey.pem
- copy the content and save it as private.pem
you can learn more about from the below link.
Load a Server Certificate and Private Key Onto Expressway
The Expressway’s server certificate is used to identify the Expressway when it communicates with client systems using TLS encryption, and with web browsers over HTTPS.
As well as these instructions, a video demonstration of the process provided by Cisco TAC engineers is available on the Expressway/VCS Screencast Video List page.
To upload a server certificate:
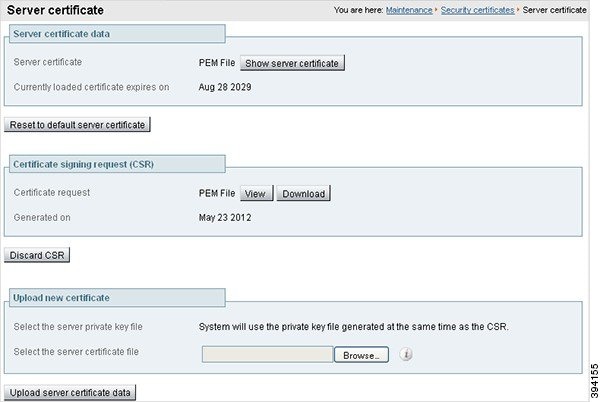
Go to Maintenance > Security > Server certificate.
Use the Browse button in the Upload new certificate section to select and upload the server certificate PEM file.
If you used an external system to generate the Certificate Signing Request (CSR) you must also upload the server private key PEM file that was used to encrypt the server certificate. (The private key file will have been automatically generated and stored earlier if the Expressway was used to produce the CSR for this server certificate.)
The server private key PEM file must not be password protected.
You cannot upload a server private key if a certificate signing request is in progress.
Click Upload server certificate data.
When you generate a CSR in X7, the application puts csr.pem and privkey_csr.pem into /tandberg/persistent/certs.
When you generate a CSR in X8, the application puts csr.pem and privkey.pem into /tandberg/persistent/certs/generated_csr.
If you want to upgrade from X7 and have an unsubmitted CSR, then we recommend you to discard the CSR before upgrade, and then regenerate the CSR after upgrade.

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2020 10:48 PM
Great answer @Nithin Eluvathingal (+5)

Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide