- Cisco Community
- Technology and Support
- Security
- Security Blogs
- What's New in NGFW FTD 7.0, ASA 9.16.1, FXOS 2.10, CSM 4.23, ASDM 7.16.1
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Cisco officially announces the release of FTD 7.0, ASA 9.16.1, FXOS 2.10, CSM 4.23, and ASDM 7.16.1 for simplifying network, workload, and multi-cloud protection to empower NetOps teams to run at DevOps speed. The 7.0 release provides immense benefits for customers and partners with software improvements and increased throughput by up to 30% for most Cisco Secure Firewalls. With reduced time to upgrade, we've made substantial improvements to policy deployment while extending deployment opportunities. Incorporating several customer and field requests, we continue to provide world-class security controls, consistent policy, and visibility, enabling customers to leverage their entire networks as extensions of their security architecture.
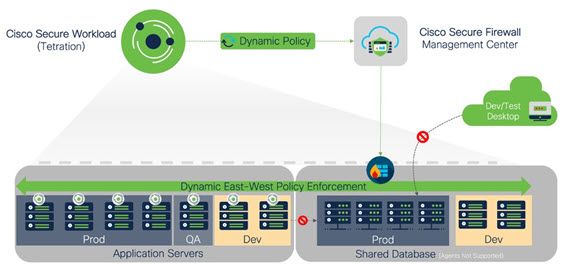
Secure Firewall and Secure Workload Integration for End-to-end Protection
Cisco offers an integrated firewall and micro-segmentation solution. The release introduces real-time, unified workload and network security, provides comprehensive visibility and control, regardless of where applications are running. Enforced and synchronized at the Secure Workload and network levels, East-West and North-South traffic is protected without managing policy and configurations at the individual device level.
The dynamic policy is pushed from Secure Workload to FMC and then downloaded to the devices managed by that FMC.
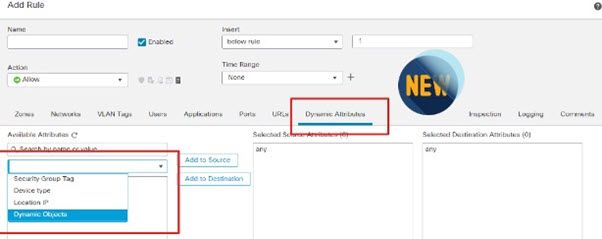
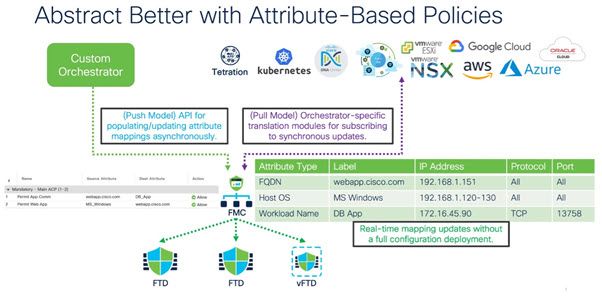
(Dynamic) Attribute Based Policy
In a dynamic multi-cloud world with changing and overlapping IP addresses, static IPs are not a reliable policy enforcement attribute. Attribute-based policy (ABP) allows customers to build dynamic objects to keep up with security demands in the hybrid cloud. Cisco Secure Dynamic Attribute Connector (CSDAC) is designed to hook into AWS, Azure, 0365, or NSX-T to pull down IP mappings to populate dynamic objects. The dynamic objects are updated in real-time and do NOT require a deployment to update.
Key Benefits:
- Enhanced security posture.
- Enables robust policies in environments where fixed IP addresses don't exist.
- Dramatically reduces operational upkeep.
Cisco Secure Managed Remote Access
(Currently available in the United States. Shortly it will be rolled out to all global customers.)
Managed Remote Access relieves customers from day-to-day remote access support so that they can focus on more strategic tasks. For customers wanting to keep VPN management in-house, Threat Defense 7.0 features enhanced VPN capabilities for many remote access use cases, building upon our experience as the global remote access leader.
FTD RA VPN Enhancements
FTD 7.0 provides many new enhancements in RA VPN functionality. It now supports DAP/Hostscan use cases and provides a programmatic way to configure it. The user can now migrate ASA RAVPN configuration to FTD.
The following lists some of the other salient features delivered in this release:
- Dynamic Access Policy (DAP)
- Host scan
- Custom Attributes: Per-App VPN, Dynamic Split Tunneling, Deferred Update
- Multi-Cert Authentication
- SAML attributes support in DAP
- SAML + VPN Load balancing
- Support for Local Authentication for RAVPN (Without Policy Enforcement) FMC: VPN GET API
Superior Threat Visibility, Analytics and Logging
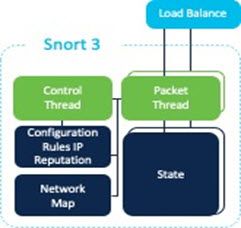
Snort 3
Snort is the de facto standard for all network intrusion detection systems. With FTD 6.7, we introduced Phase 1, support for CDO and FDM-managed FTD devices. Now available with FMC, the new human-readable rules simplify IPS, and the unique architecture maintains performance while running more rules, improving threat defense. New HTTP/2 support expands Snort 3 visibility, and new automated rule migration streamlines upgrades for existing firewall and dedicated IPS users. Two new protocol parsers allow inspection of the tag values for Siemen's S7 and IEC 60870-5-104 and potential expansion in that market sector for industrial customers.
Snort 3 is now available in Cisco Meraki MX, and Umbrella SIG cloud-delivered firewall.
- Improved efficacy
- Expanded protocol coverage
- Faster and easier rule updates
- Performance improvements
Superior Performance
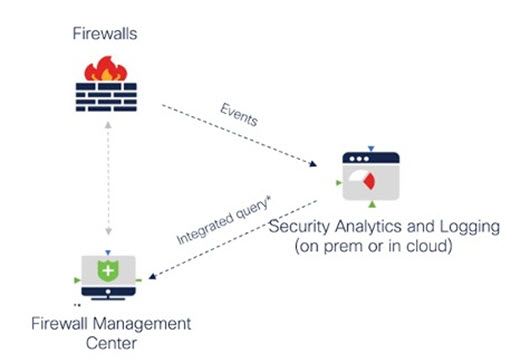
Scalable Eventing, Logging & Analytics
The Cisco Security Analytics & Logging (SAL) on-premises functionality allows FMC to log events externally and view them directly.
SAL now offers a tightly integrated and dedicated solution for FMC to log events at a massive scale. Optimizing the performance of FMC, administrators can store firewall logs at an event rate up to 5x faster FMC. It provides administrators a larger event scale and retention. Also provides the ability to query and run reports on the data (local or remote) directly in the FMC without pivoting to another console. Configuring integration and changing historical syslog configs just got easier with the configuration wizard.
Key Benefits:
- Connection events sent to a dedicated logging solution allow the FMC to perform threat detection.
- Administrators now have a single interface to query events directly in the FMC, providing historical data during investigations.
- An affordable, integrated option for the FMC when compliance demands the storage of events for x-number of days.
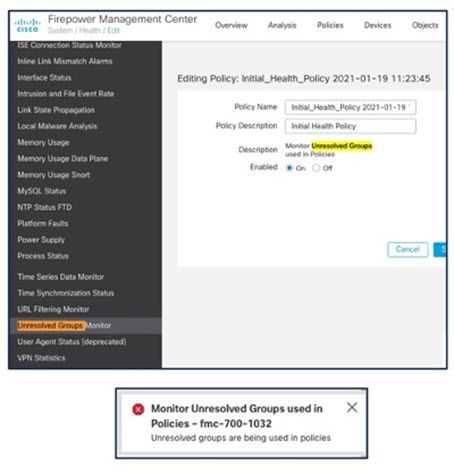
Cross Domain Groups
Typically, customers deployed an AD (Active Directory) with a forest containing a collection of Trees containing Domains. For more information, see Domain Trees and Forests. Until now, Firepower products understood a single Domain represented in a single realm and could not represent a group of users outside the current Domain from where they were synced (essential for group-based policy). Also, in environments where multiple Administrators manage the FMC platform, overriding configuration changes create confusion and reduce confidence in deployment.
Customers can now perform the following:
- Recognize established relationships between domains in Microsoft AD/LDAP forest.
- Learn any user identity and group membership from any domain/child domain.
- Receive notifications about users that have a reference for an external domain.
- Preview pending policy deployment changes to configurations in Realms and Realm Sequences configurations. It helps administrators predict how a device will function after policy deployment (bonus: this functionality offers enterprise customers audit capabilities).
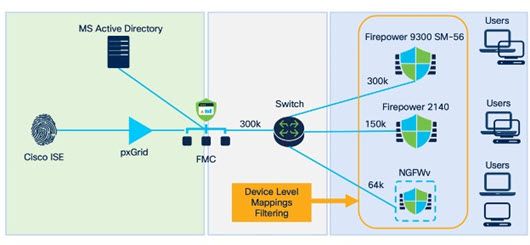
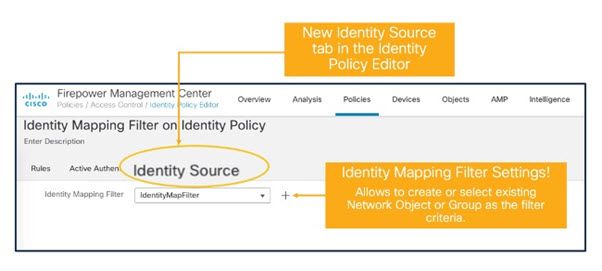
Device Level Identity Filtering
Previously, the filtering of identity mappings was possible between ISE and FMC but not FMC and FTD, creating a bottleneck, overloading lower-end devices with the total number of identity mappings/bindings. The new FMC Identity Policy subnet filter configuration allows users to limit identity mappings to those used by FTDs and control User-IP, SGT-IP, and dynamic object mappings are shared from FMC to individual managed devices.
Key Benefits:
- Achieve lower usage of Snort Identity Memory by installing only identity mappings from subnets monitored by a specific managed device (FTD).
- Utilize only required Identity Mappings (User-IP, SGT-IP, Dynamic Object Mappings) on the managed devices (FTD).
- Manage all types of devices (low/mid/high-end) with a single management platform (FMC).
- Control the total number of user identity mappings per device based on the platform's total number of recommended bindings.
Integrated Platform Approach with SecureX
The integration with Secure X closes the gap between active defense and incident response (accelerating resolution with less effort). It demonstrates the promise of a complete security lifecycle solution based on a truly open platform.
The FMC-hosted SecureX ribbon for investigation context enables the SecOps team to pivot instantly from an event that is seen in the firewall and the SecureX platform that correlates threats across the Cisco Secure portfolio. Customers can build flexible, cloud-based automation between FMC and third-party tools like ServiceNow and Tufin. FMC uses SSE event push to SecureX for use cases and scenarios that are typically used by threat hunting teams. Also, FMC API execution can use SSE-based automation to cover other use cases.
Key Benefits:
- Reduced time to detect, contain, and mitigate threats.
- Orchestrate pre-built playbooks, simplifying incident response.
- Enhance collaboration between NetOps, ITOps, and SecOps.
- Strengthen breach defense unifying visibility with alerts correlated and prioritized from other integrated Cisco Secure and third-party solutions.
- Optimize network performance, automating VPN capacity management to facilitate continued remote worker productivity.
Lina Static Analysis
The FTD 7.0 release improves Lina static analysis to prevent quality issues, shorten development and testing cycles to identify problems earlier, and save engineering effort.
Installs, Upgrades and Rule Updates
The user experience of upgrades is enhanced, and the FTD upgrade package size is reduced, which resulted in improved stability, reliability, and time to upgrade FTD standalone. The scripts and first boot have been enhanced for FTDv and increased the number of concurrent upgrades.
Global Search - Enable Semantic Search Index (IPv4)
Global search allows using wildcard characters at a central location for customers to search text and navigate to specific components easily from the search results. You can easily find information about policy names, descriptions, rule names or comments, object names, and descriptions.
Secure Firewall Cloud Native
Secure Firewall Cloud Native provides elastic and scalable security services, especially in public cloud deployments. It aims to simplify the task. Leveraging Kubernetes for orchestration, autoscaling, autohealing, and real-time responsiveness to capacity changes, it's now available in AWS to simplify VPN deployment and management. Expect other security services to follow. It dynamically scales with throughput requirements, simplifies provisioning and management.
ASAv and FTDv - New Platform
You can now deploy FTDv on 16 core virtual machines, providing increased NGFW performance (up to 15.5 Gbps on ESXi/KVM) applicable for both private and public clouds.
The Cisco Adaptive Security Virtual Appliance (ASAv) and Firepower Threat Defense virtual (FTDv) can now be deployed in an OpenStack environment. OpenStack is a set of software tools for building and managing cloud computing platforms for public and private clouds and is tightly integrated with the KVM hypervisor. Enabling OpenStack platform support for ASAv allows customers to run Cisco ASAv/FTDv on open-source cloud platforms. The Firepower Management Center virtual (FMCv) can also be deployed on OpenStack and configured to manage virtual and physical Firepower devices.
As the hybrid cloud trend continues to grow, Enterprises are building out their private cloud environments with 'Hyper Converged Infrastructure' (HCI). The FTDv and FMCv are now validated to run on Cisco Hyperflex and Nutanix AHV environments.
This release also includes a tiered licensing capability for FTDv providing a low entry price point and catering to different performance requirements. The tiers start from 100Mbps and go up to 15.5 Gbps (NGFW throughput). The performance tiers can be configured by using FMC or Firepower Device Manager (FDM).
Enhanced ACI integration
Enhanced ACI firewall integration updates include the FMC Endpoint Update application version 1.2 (Docker container), which adds support for multi-site and multi-domain. Continued Device Package support validates release version compatibility with supported platform setups. Device script handlers interface with the devices using its REST API or CLI interface.
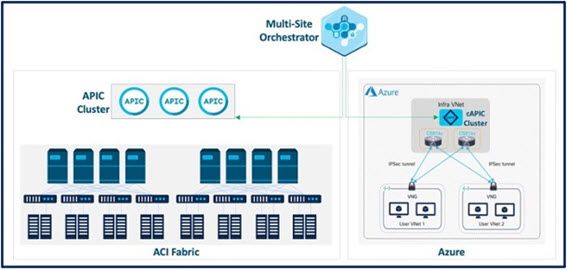
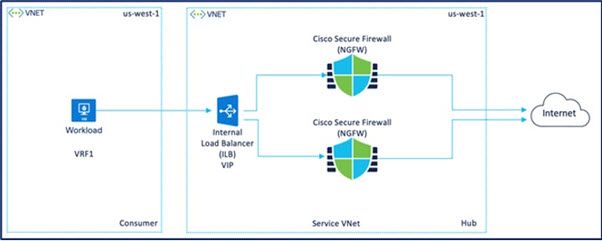
Cisco Secure Firewall Support with cAPIC in Azure
Cisco Cloud APIC runs natively on supported public clouds and translates all the policies that are received from MSO and programs them into cloud-native constructs such as VNets (Virtual Network), application security groups, network security groups, outbound rules, inbound rules, etc. This new solution brings a suite of capabilities to extend on-premises data centers into true hybrid cloud architectures, helping drive policy and operational consistency regardless of where applications reside. Also, it provides a single point of policy orchestration across hybrid environments, operational consistency, and visibility across clouds.
Cisco ASA and FTD firewalls are integrated as "unmanaged" firewalls (Cisco ASAv and FTDv/NGFWv) devices into existing ACI deployments. At the same time, current ACI contracts can be easily leveraged for enforcing security policies.
Unified Real Time Event Viewer
Security teams face information overload. Firewalls and IPS devices are generating higher volumes of events. Inefficient tools split data between multiple pages or lack the necessary context for quick resolution magnifying the problem. Navigating between different views and following unclear connections between events confuses customers and consumes valuable time.
Unified Event Viewer can stream data from sensors, correlate different events based on host identity, flows, or other connecting attributes, making it possible to complete incident investigations more quickly. At the same time, advanced content filtering helps customers drill down to specific incident details.
Cisco Secure Firewall YouTube Channel
The Cisco Secure Firewall YouTube Channel has been placed within the FMC UI and features three playlists:
- Cisco Secure Firewall 7.0 Release
- Snort 3
- Cisco Secure Firewall Cloud Native (SFCN) 1.0 Release
The main track shows the updates and new features available, while the Snort 3 track contains in-depth overviews of Snort 3 functionality and how it compares to Snort 2. Finally, the SFCN track showcases our newest product solution.
Secure Firewall GitHub Repository & DevNet Portal
Cisco introduces the Secure Firewall Developer Page and a new Secure Firewall GitHub repository. Newly created resources, templates, and videos guide customers on consuming Infrastructure as a Code with security baked-in. Our teams are updating training labs, sandbox environments, and more automation scripts, all coming soon.
Secure Firewall Essentials
Introducing Secure Firewall Essentials portal, a centralized repository offering a best practice approach to Cisco Secure Firewall configuration. Check out the Cisco Secure Firewall solutions collateral, step-by-step guides, and new feature highlights from the TME team.
Read the 7.0 Release Notes for more information, including a complete list of features available.
See the NGFW Community Page for documentation.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: